- Course
ADFS2 and WIF 3.5
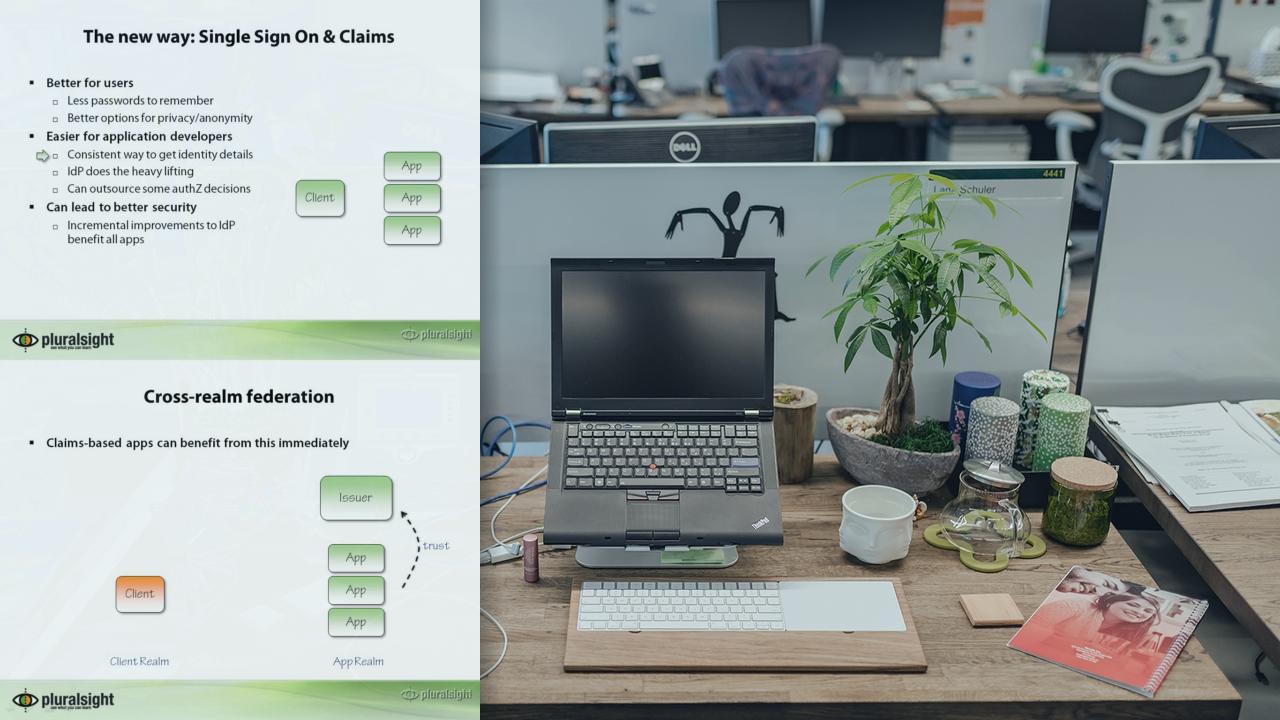
Explains Federated SSO and the "Claims Aware" programming model in ASP.NET: the Zen, architecture, implementation, setup, customization and protocols.
- Course
ADFS2 and WIF 3.5
Explains Federated SSO and the "Claims Aware" programming model in ASP.NET: the Zen, architecture, implementation, setup, customization and protocols.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
The course contains an introduction to Single Sign-On. An in depth explanation of the Windows Identity Foundation (WIF) and the ADFS version 2 server. In depth means: bits and bytes of the HTTP requests and responses, HttpModules, and customization. The analysis of the protocol is done with Fiddler2 and code analysis with Reflector. It also covers the Claims Language, Metadata and SAML2 partners. One module walks through some common scenarios and shows with code and configuration how to implement them.

