- Course
AngularJS Security Fundamentals
AngularJS has achieved enormous popularity in a very short amount of time, but developers keep asking - what are the security implications? This course helps those building apps on client side frameworks understand where the risks lie and how to mitigate them.
- Course
AngularJS Security Fundamentals
AngularJS has achieved enormous popularity in a very short amount of time, but developers keep asking - what are the security implications? This course helps those building apps on client side frameworks understand where the risks lie and how to mitigate them.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
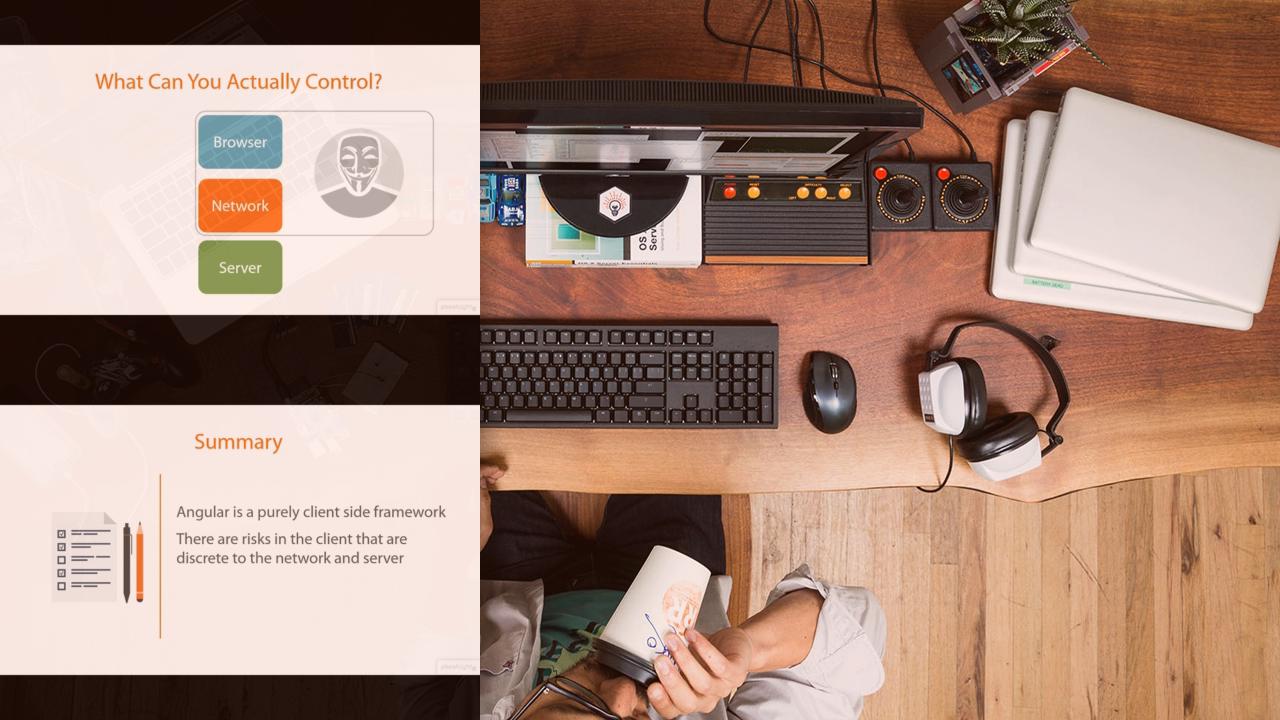
Client side frameworks such as AngularJS have become enormously popular due to their ability to streamline the development process and make more responsive web applications by moving workload from the server to the browser. With the popularity and enthusiasm around these frameworks also comes confusion about their security profiles and associated risks. Often, when developers build client apps with server back ends they approach the application as though they control the entire ecosystem. Assumptions are often made that the client they built will only ever talk to the server side APIs they built in the way they designed them. This view often overlooks the risk of an attacker circumventing the client controls and executing calls directly against the server side A9PI outside the intended scope of the application. Much of this course is about helping developers understand where the security boundaries of client side frameworks begin and end. It does this by demonstrating common implementation patterns using Angular and illustrating where security weaknesses may be introduced. It also highlights specific defenses implemented by Angular, and demonstrates the mechanics of how they work, and how they may be misconfigured to introduce risks.

