- Course
Cisco CyberOps: Analyzing the Network
Cybersecurity concepts are fundamental pieces of knowledge necessary to have a career in the industry. This course will detail the network data that we can use for cyber operations and how to use it within your environment.
- Course
Cisco CyberOps: Analyzing the Network
Cybersecurity concepts are fundamental pieces of knowledge necessary to have a career in the industry. This course will detail the network data that we can use for cyber operations and how to use it within your environment.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
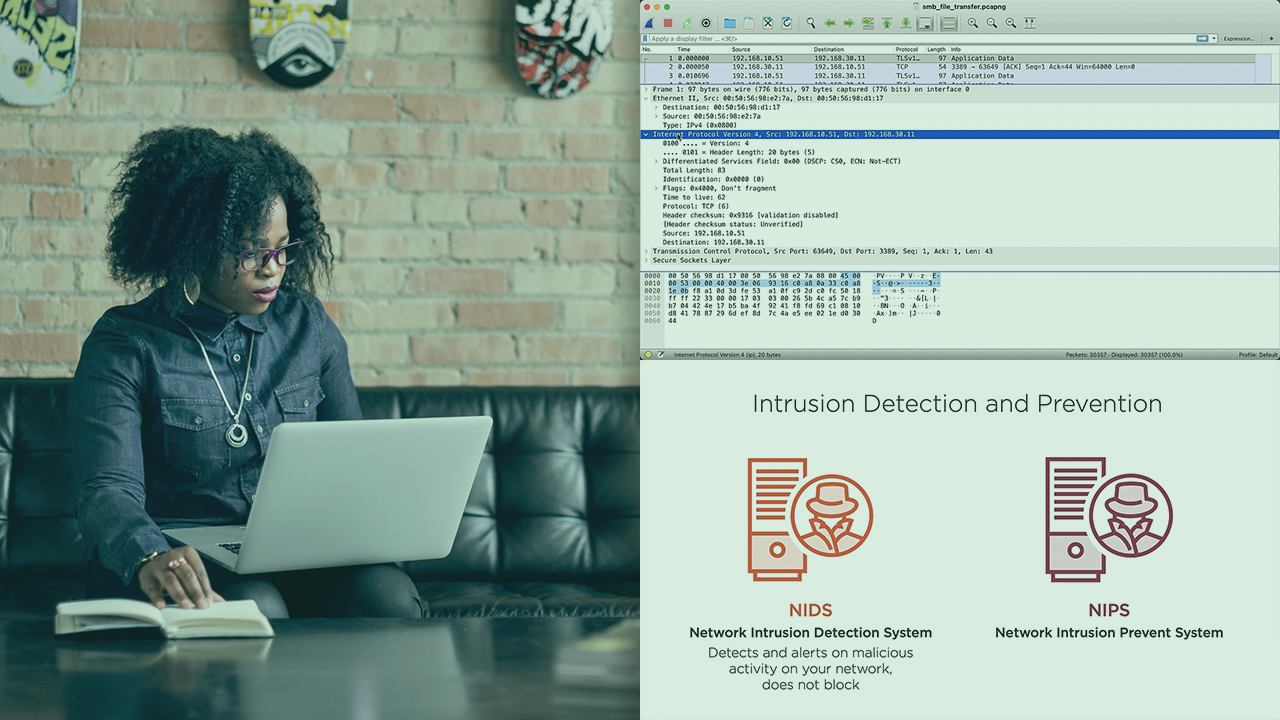
There is a tremendous skill shortage in the cybersecurity sector of IT that is hindering operations at organizations. In this course, Cisco CyberOps: Analyzing the Network, you’ll learn the some of the concepts needed to start your journey into the SOC operations realm. First, you’ll learn about the event sources and the data that they provide. Then, you'll dive into inspecting various network data types and see what they provide, highlighting NetFlow and raw packet data. You’ll break down datagrams and identify the key elements of the raw data, as well as interpret protocol headers. Finally, you’ll take a look at alerts and events and how to interpret them. When you’re finished with this course, you’ll be one step closer to having a solid understanding of cybersecurity concepts and be able to continue learning how to identify problems and perform tasks in a SOC environment.
Cisco CyberOps: Analyzing the Network
-
Seeing Threats from the Network | 6m 17s
-
Network Data Sources: Syslog and Telemetry | 4m 10s
-
Examining Network Data Sources | 5m 14s
-
Examining More Network Data Sources | 5m 42s
-
Other Network Data Sources | 5m 23s
-
Examining Additional Network Data Sources | 6m 21s
-
Seeing the Raw Traffic | 5m 24s
-
Impacts of Positive and Negative Detections | 3m 37s


