- Course
Getting Started with Cisco Stealthwatch
Security teams need a complete understanding of potential security threats, both internal and external, that could disrupt the network. Stealthwatch can monitor networks for potential threats, but before it can, you need to know how to install and configure it.
- Course
Getting Started with Cisco Stealthwatch
Security teams need a complete understanding of potential security threats, both internal and external, that could disrupt the network. Stealthwatch can monitor networks for potential threats, but before it can, you need to know how to install and configure it.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
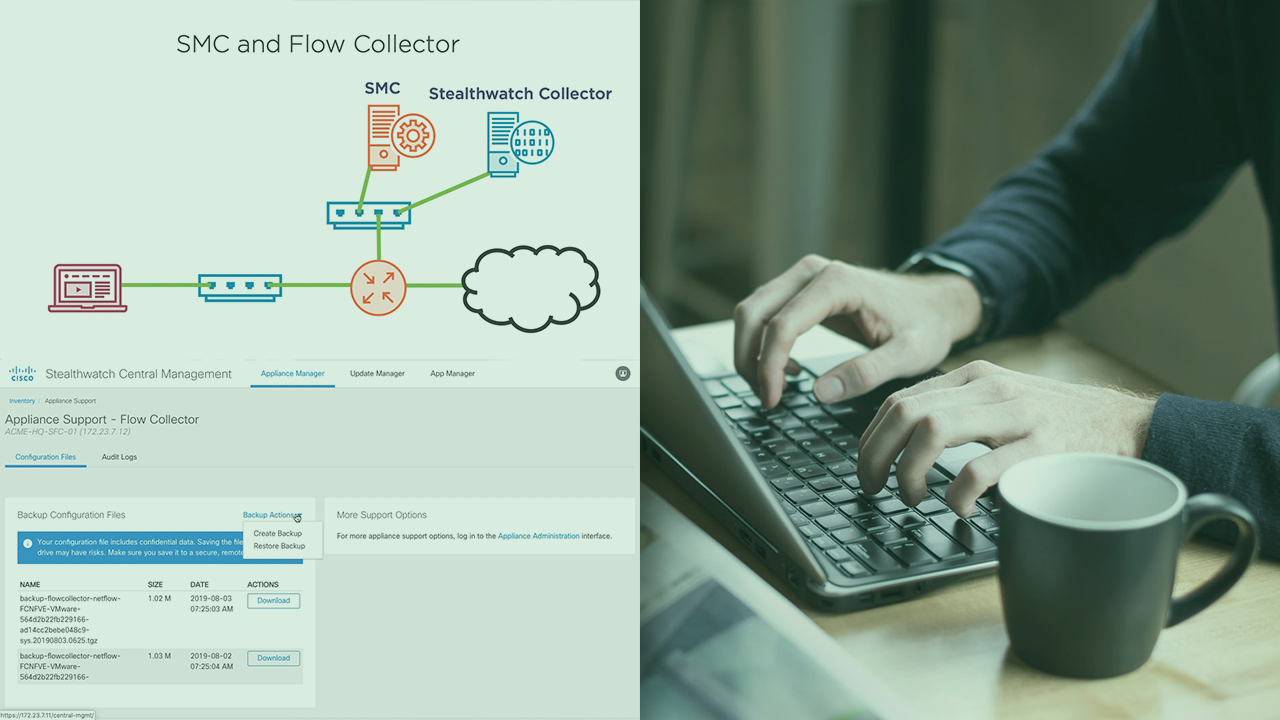
Attacks on enterprise networks, whether they are a denial of service attacks or malware, have the potential to cause a lot of disruption. Moreover, attacks can come from an internal source in addition to external sources. SOC teams need a tool that will alert them when an attack is in progress and help them pinpoint the attacker and the target. SOC teams need Stealthwatch. In this course, Getting Started with Cisco Stealthwatch, you will not only learn how to install the various Stealthwatch components, but you will also discover how to configure and tune Stealthwatch. First, you will begin by looking at how Stealthwatch looks for threats. Next, you will go through how to install a Stealthwatch Management Console and Flow Collector before learning how to enable NetFlow on IOS-based network devices. Finally, after learning how to tune Stealthwatch, you will look at how to back up and upgrade a Stealthwatch system. When you’re finished with this course, you will have the skills and knowledge of Stealthwatch needed to support a Stealthwatch system on an enterprise network.

