- Course
CISSP® - Security Operations
This course covers the 7th domain of the CISSP. You'll learn about the day to day operational duties, best practices, and security concepts that security professionals will need to be familiar with prior to attempting the CISSP examination.
- Course
CISSP® - Security Operations
This course covers the 7th domain of the CISSP. You'll learn about the day to day operational duties, best practices, and security concepts that security professionals will need to be familiar with prior to attempting the CISSP examination.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
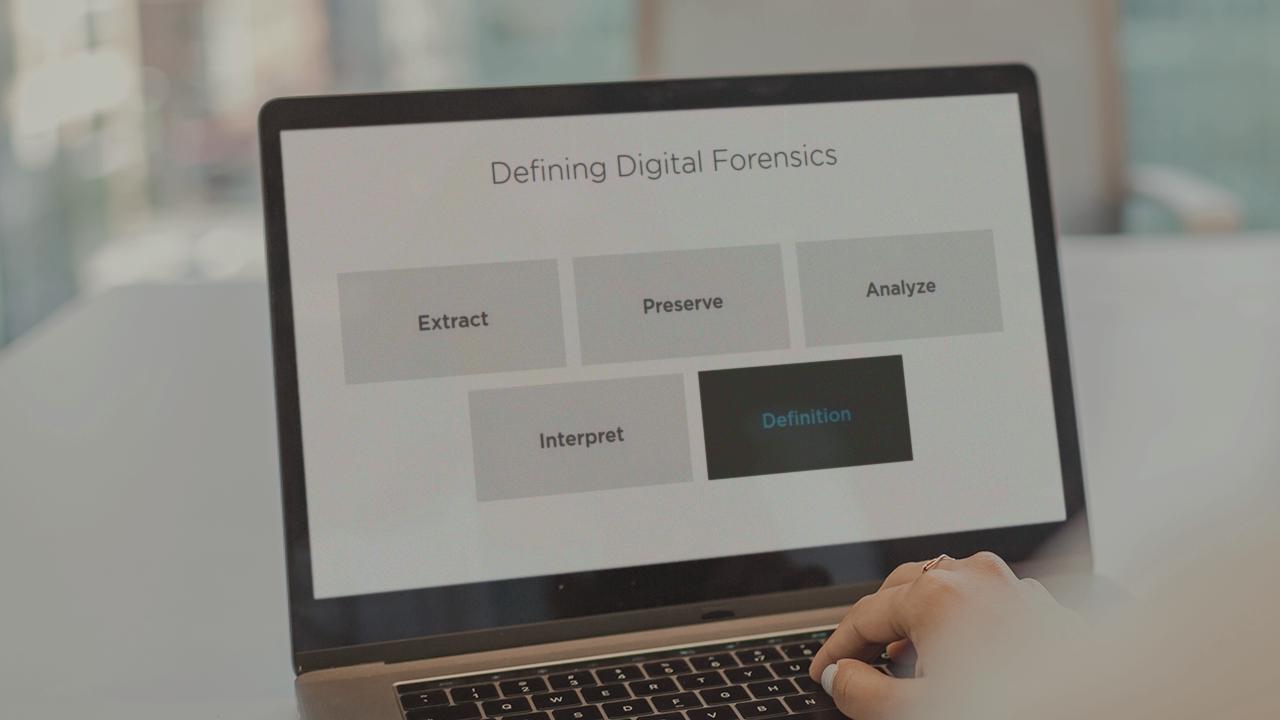
This course, CISSP® - Security Operations, covers the wide breadth of topics within the Security Operations domain of the CISSP. This includes activities such as evidence collection and handling, investigative techniques and types, monitoring and logging activities such as intrusion detection and prevention, event management, and egress monitoring. In addition to this, there will also be a focus on securing the provisioning of resources, understanding foundational security operational concepts such the information lifecycle, and job rotation. The course also covers topics such as resource protection, incident management, operation of preventative measures such as firewalls, implementing a patch management program, understanding how to implement change management, and learning about recovery strategies. By the end this course, you should be familiar with a broad spectrum of topics that are covered within the Security Operations domain of the CISSP. This course will provide you with the background information that you will need when addressing questions related to Security Operations.

