- Course
Command and Control with Empire
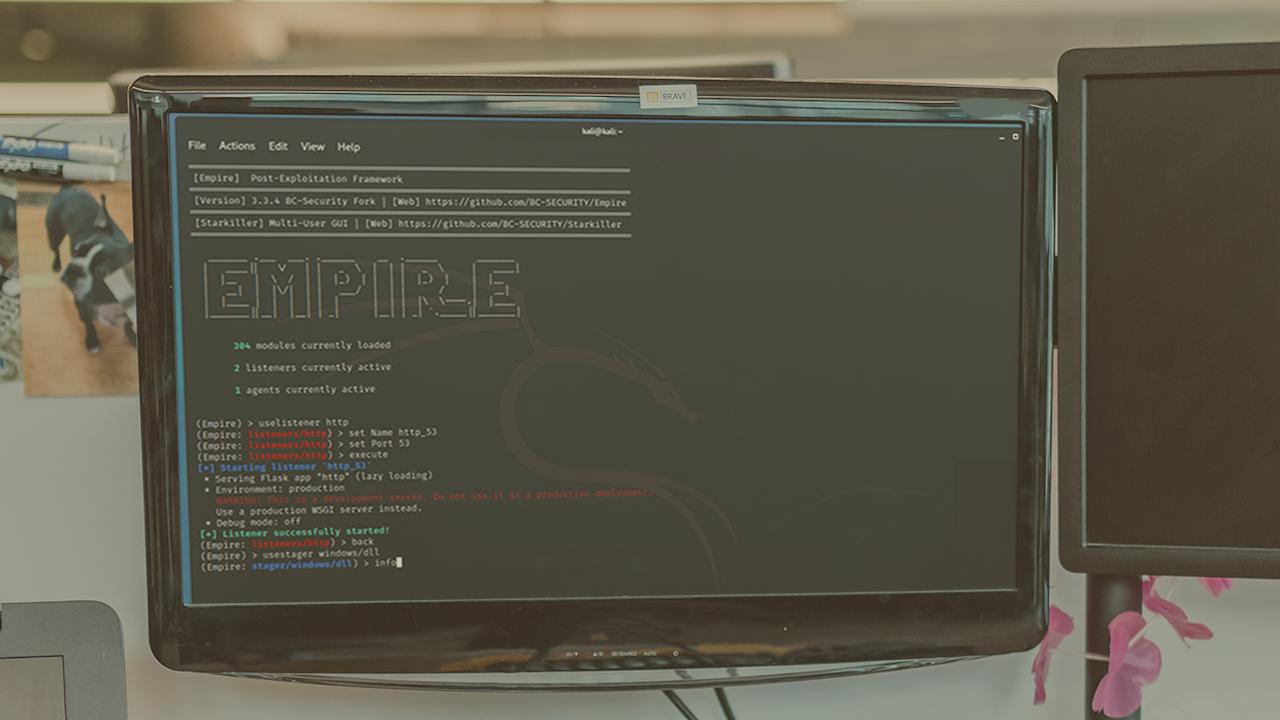
PowerShell has quickly become the standard in enterprise networks. In this course you will learn how to leverage Empire to perform command and control techniques during a red team engagement.
- Course
Command and Control with Empire
PowerShell has quickly become the standard in enterprise networks. In this course you will learn how to leverage Empire to perform command and control techniques during a red team engagement.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Are you looking to use Empire in a red team engagement? In this course, Command and Control with Empire, you’ll learn how to utilize Empire for command and control in a red team environment. First, you’ll see how to leverage multi-hop proxies for C2. Next, you’ll learn to apply file upload capabilities and registry commands to establish remote access. Finally, you’ll explore to simulate establishing a C2 over a non-standard port. When you’re finished with this course, you’ll have the skills and knowledge to execute ingress tool transfer (T1105), remote access software (T1219), non-standard port (T1571) and multi-hop proxy (T1090.003) using Empire.

