- Course
Command and Control with Merlin
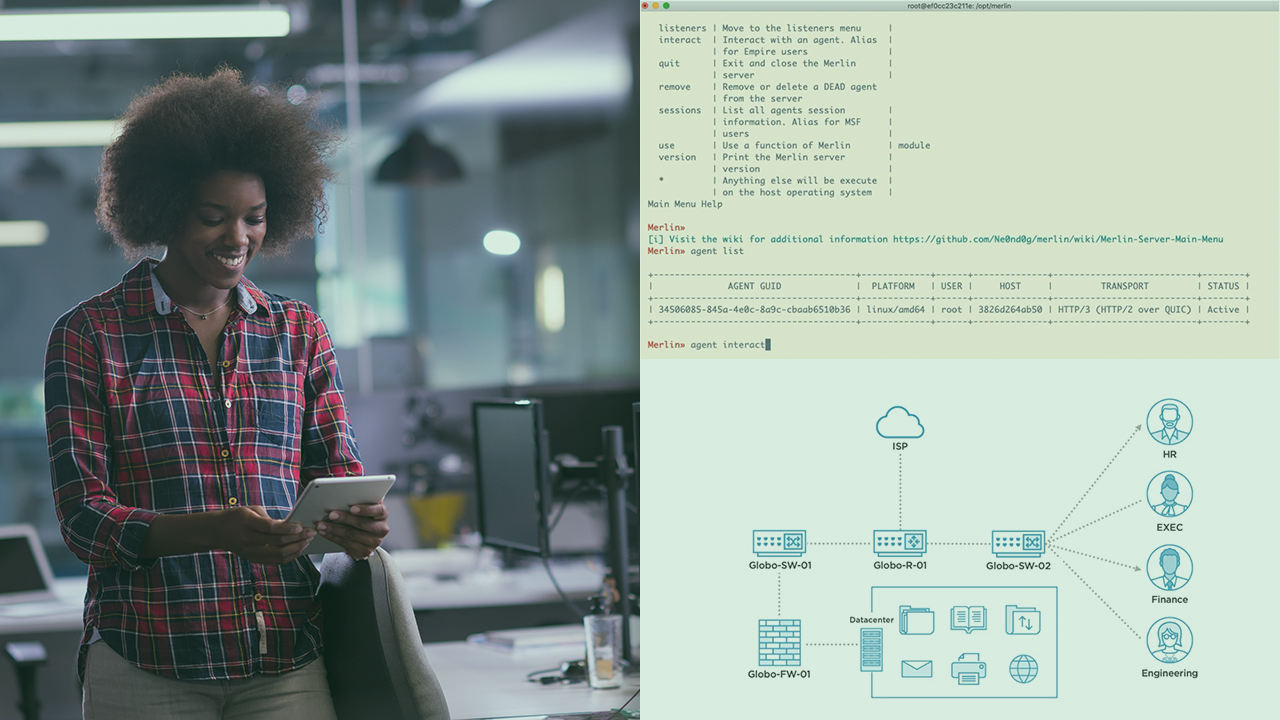
In this course, you will learn Command And Control using Merlin. Merlin’s “magic” is in the usage of modules (for attack automation), HTTP/3 (for evading packet inspection), and Golang (for cross-compiling agents on multiple Operating Systems).
- Course
Command and Control with Merlin
In this course, you will learn Command And Control using Merlin. Merlin’s “magic” is in the usage of modules (for attack automation), HTTP/3 (for evading packet inspection), and Golang (for cross-compiling agents on multiple Operating Systems).
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Want to learn how a C2 server can be leveraged to steal a database backup? If so, you’re in the right place! In this course, Command and Control with Merlin, we’ll cover how to utilize Merlin to execute data exfiltration in a red team environment. First, you’ll witness how Merlin evades network packet detection via the HTTP/3 protocol. Second, you’ll use Merlin’s HTTP/3 functionality to upload a recon script. Finally, you’ll use the results of the recon script to exfiltrate a database backup to the Merlin C2 server. During each step of the process, we’ll see what Merlin attacks are discovered by Wazuh (a host-based intrusion detection system) and Suricata (a network-based intrusion detection system). No previous Wazuh or Suricata experience is required. When you’re finished with this course, you’ll have the skills and knowledge to execute these techniques: Exfiltration Over C2 Channel (T1041), Ingress Tool Transfer (T1105), Application Layer Protocol (T1071) using Merlin.

