- Course
Command and Control with Pupy
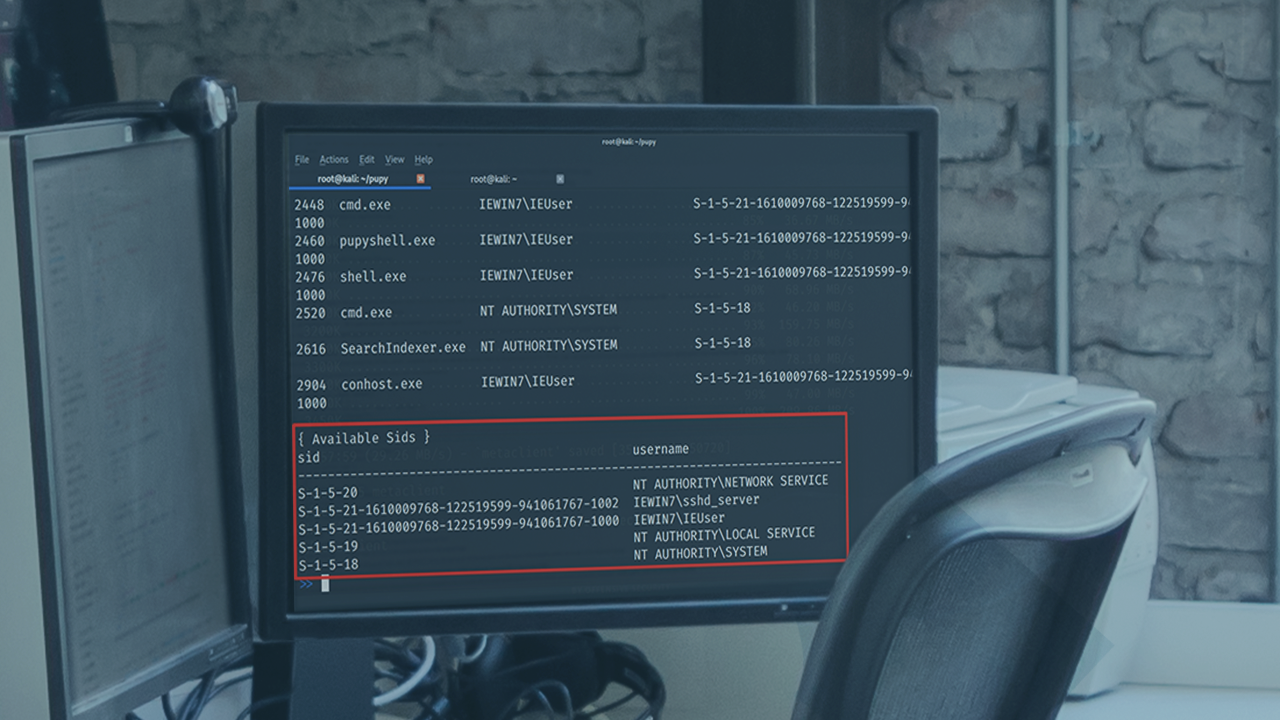
Learn how to use the Pupy server to connect to exploited clients over different encryption protocols and use these sessions to run additional attacks, dump credentials, and collect information.
- Course
Command and Control with Pupy
Learn how to use the Pupy server to connect to exploited clients over different encryption protocols and use these sessions to run additional attacks, dump credentials, and collect information.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Are you looking for a tool that can help you manage your target workstations after you exploited them? In this course, Command and Control with Pupy, you will gain the ability to manage target sessions, collect information, and run additional attacks from a single interface. First, you will learn how to generate client files in Pupy. Next, you will discover how to use different encryption protocols in Pupy. Finally, you will explore how to capture information from targets using Pupy. When you are finished with this course, you will have the skills and knowledge needed to manage exploited targets with Pupy.

