- Course
CompTIA Security+ (SY0-401) Application, Data, and Host Security
CompTIA Security+ (2014 Objectives): Domain 4 - Application, Data, and Host Security.
- Course
CompTIA Security+ (SY0-401) Application, Data, and Host Security
CompTIA Security+ (2014 Objectives): Domain 4 - Application, Data, and Host Security.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
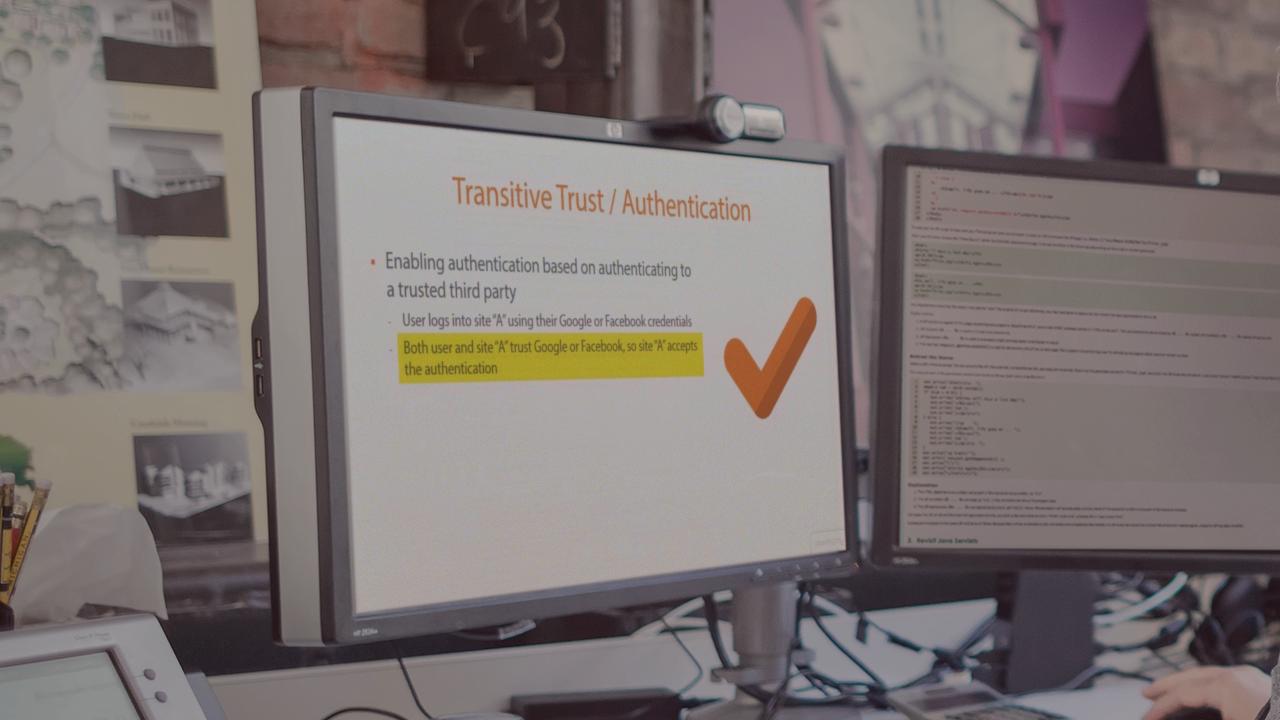
This course covers the material that comprises Domain 4.0 of the CompTIA Security+ SY0-401 certification exam. Topics include application security concepts such as fuzzing, cross-site scripting, cross-site request forgery, application and database hardening, device security, encryption, data-wiping, SCADA and embedded systems security, virtualization and cloud security concepts, mobile device security, and the various methods used to implement security best practices.

