- Course
Credential Access with Cain & Abel
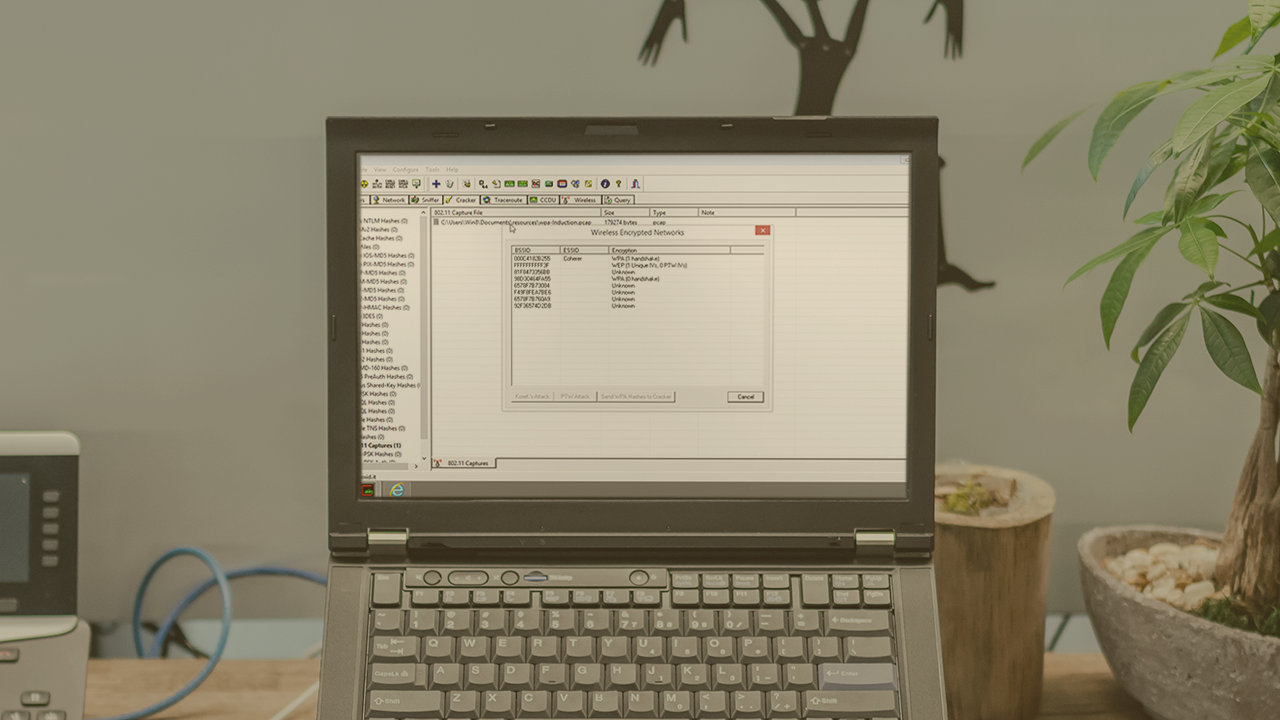
From manipulating network traffic to cracking user credentials, this course will give you the skills and understanding to further your red teaming objectives towards exploitation, credential access, and lateral movement.
- Course
Credential Access with Cain & Abel
From manipulating network traffic to cracking user credentials, this course will give you the skills and understanding to further your red teaming objectives towards exploitation, credential access, and lateral movement.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Cain & Abel is a versatile tool for the Windows operating system which can help further your red teaming objectives with techniques ranging from manipulating network traffic to cracking passwords using brute force and cryptanalysis attacks. In this course, Credential Access with Cain & Abel, you will gain the ability to access credential sets in a victim network. First, you will learn to perform network reconnaissance from the Windows operating system. Next, you will discover how you can use a man-in-the-middle attack to access the credentials transmitted between victims on a network. Finally, you will explore how to remotely exploit a victim for harvested credentials which can then be cracked by the tool suite. When you are finished with this course, you will have the skills and knowledge of Cain & Abel needed to access valid credential sets and move through a network during an attack engagement.

