- Course
Credential Access with Responder
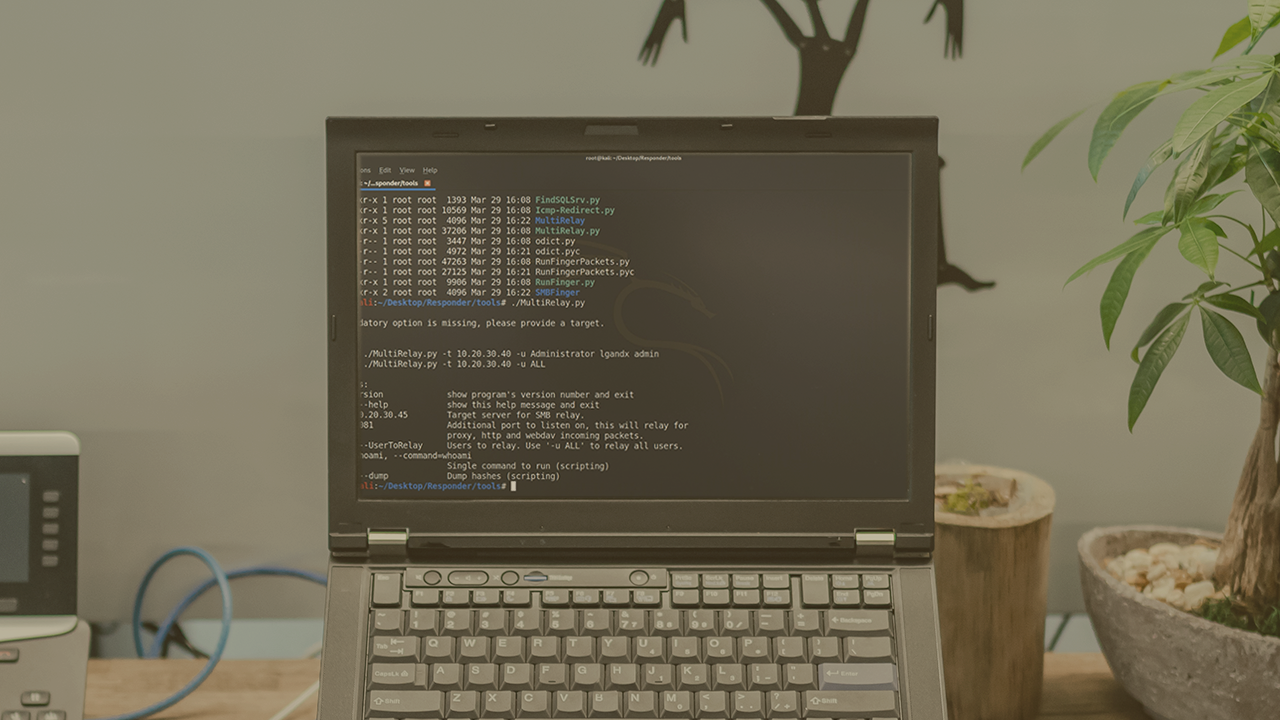
After getting initial access in a network, your next task is to move laterally and escalate privileges. In this course, you will see the Responder tool which allows you to exploit vulnerabilities on the LLMNR and NBT-NS protocols to get credentials
- Course
Credential Access with Responder
After getting initial access in a network, your next task is to move laterally and escalate privileges. In this course, you will see the Responder tool which allows you to exploit vulnerabilities on the LLMNR and NBT-NS protocols to get credentials
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
One of the main objectives on a red team engagement is to get access to several user accounts (lateral movement) as well as administrator accounts (privilege escalation). After getting initial access to the internal network, you can launch several attacks to harvest credentials. In this course, Credential Access with Responder, you will explore one of the most important tools for lateral movement and privilege escalation, the Responder tool - a LLMNR, NBT-NS, and MDNS poisoner developed by Laurent Gaffie. First, you will exploit vulnerabilities on the LLMNR protocol. Then, you will use NBT-NS and MDNS protocols to gather credentials of domain users. Finally, you will learn not only how to get NTLM hashes, but also how to crack them to get plain text passwords and how to use those hashes in pass-the-hash attacks. By the end of this course, you will know two important tactics from the MITRE ATT&CK framework: LLMNR/NBT-NS Poisoning and Relay (T1171) and Network Sniffing (T1040).

