- Course
Credential Access with THC Hydra
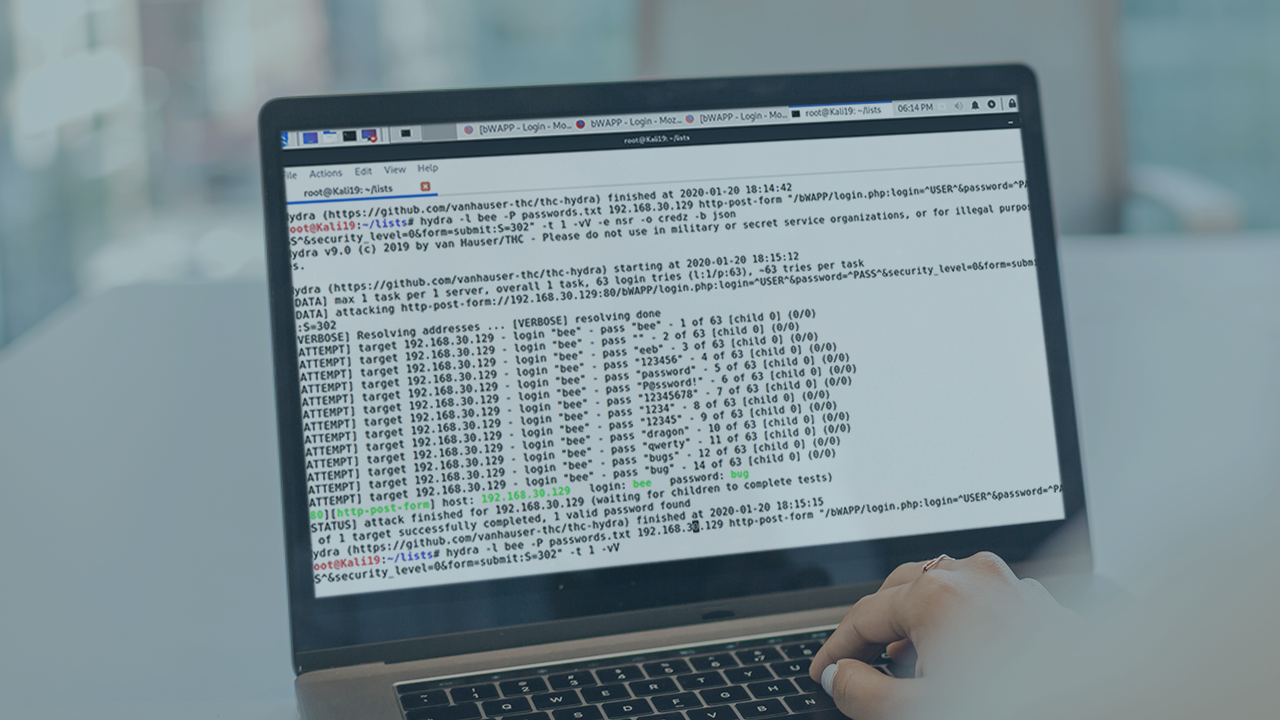
THC Hydra is a fast and powerful parallelized network login cracker with support for a wide variety of network protocols. Skill up your brute forcing techniques by leveraging THC Hydra to identify weak passwords.
- Course
Credential Access with THC Hydra
THC Hydra is a fast and powerful parallelized network login cracker with support for a wide variety of network protocols. Skill up your brute forcing techniques by leveraging THC Hydra to identify weak passwords.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
There's no way around it - people are going to use weak passwords. THC Hydra will help you identify these passwords so that you can then use the information towards Red or Blue Teaming efforts. In this course, Credential Access with THC Hydra, you will learn how to brute force network logins. First, you will see where THC Hydra fits into the kill chain and the Mitre ATT&CK framework. Next, you will discover how the flexibility of THC Hydra can assist you in cracking passwords for various network protocols. Finally, you will explore how to leverage the password cracking capabilities of THC Hydra towards your own penetration testing or password strength assessment activities. When you are finished with this course, you will have the skills and knowledge needed to efficiently use THC Hydra towards your password cracking efforts.

