- Course
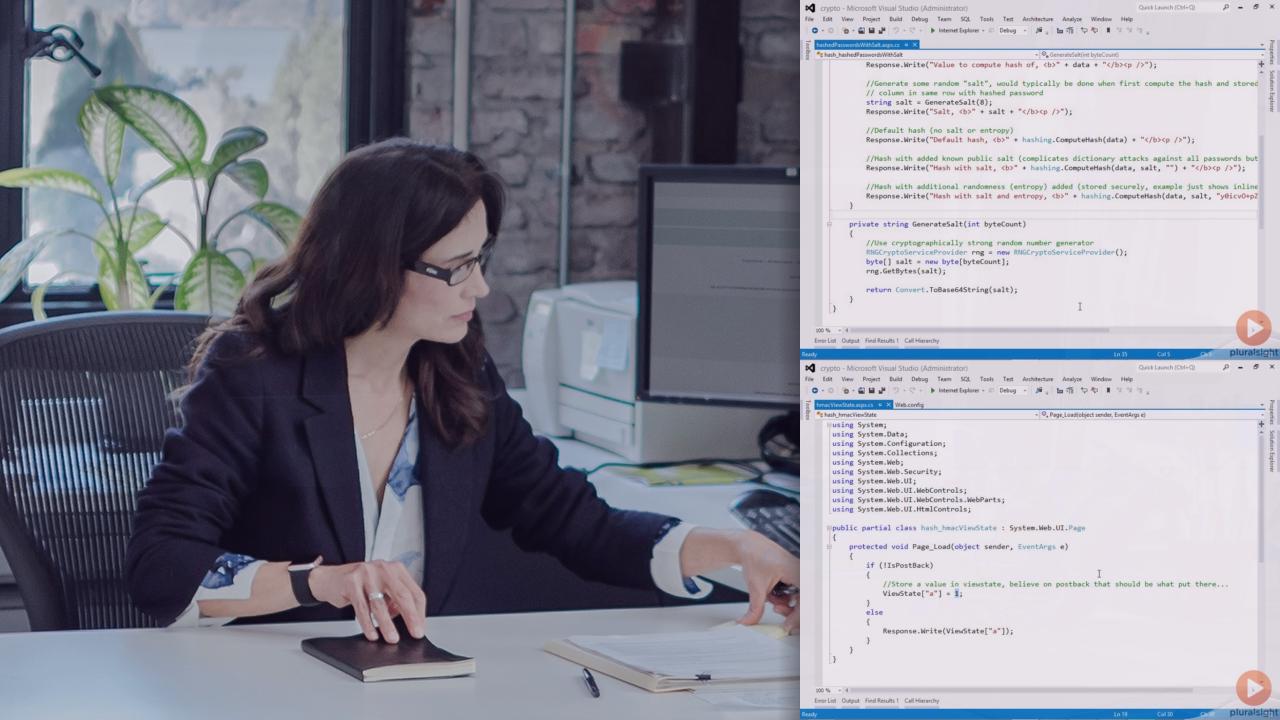
Introduction to Cryptography in .NET
Learn how to leverage cryptograpy to secure computer systems.
- Course
Introduction to Cryptography in .NET
Learn how to leverage cryptograpy to secure computer systems.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Walk through the "black art" of cryptography, including public/private and symmetric encryption, hashing, digital signatures, and a dash of salt. Review the basics of cryptography and what techniques are appropriate for various situations. Discover practical techniques for securing content received on public web sites. Review .NET classes to use for cryptography, how ASP.NET uses cryptography, and how to protect sections of the web.config file.

