- Course
Cryptography Principles for IT Professionals and Developers
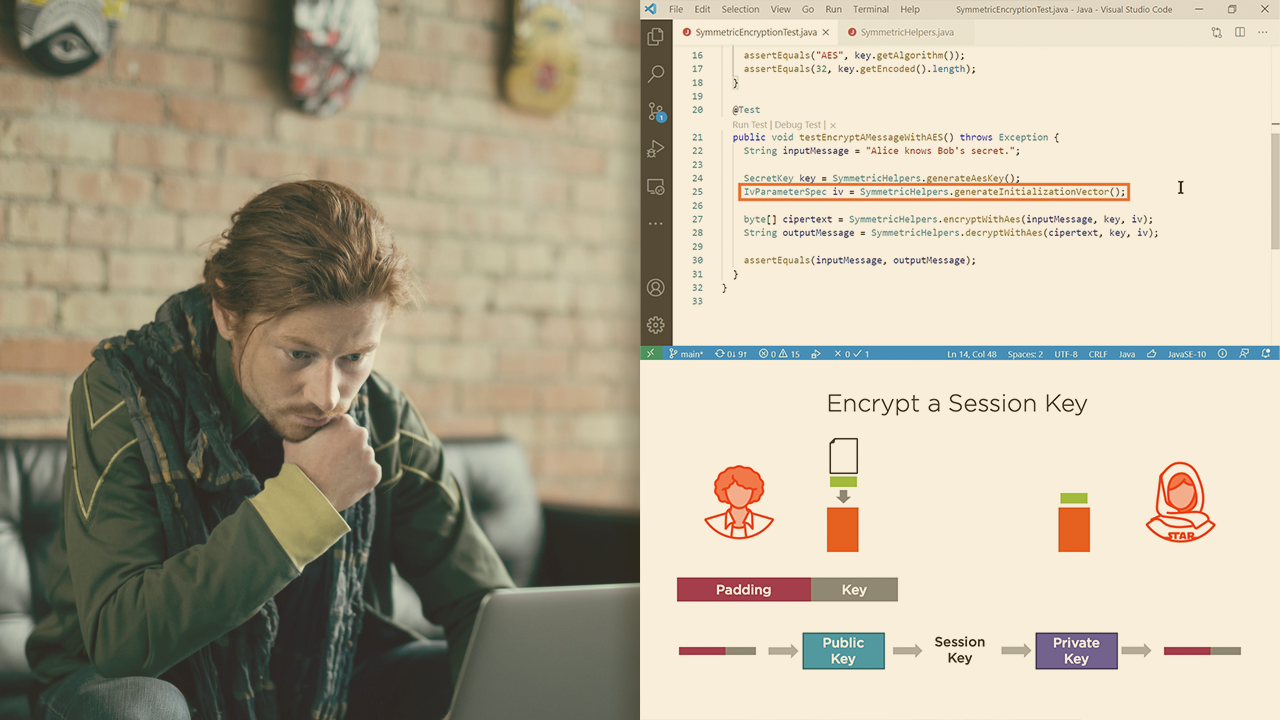
Although it appears complicated, cryptography is based on simple mathematics. This course will guide you through the theory and application of cryptography so that you will understand for yourself when it is used incorrectly and how to use it well.
- Course
Cryptography Principles for IT Professionals and Developers
Although it appears complicated, cryptography is based on simple mathematics. This course will guide you through the theory and application of cryptography so that you will understand for yourself when it is used incorrectly and how to use it well.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Cryptography is at the heart of all information security, from administering infrastructure to writing secure code. To be effective, you need to understand how cryptography works and how far it can be trusted. In this course, Cryptography Principles for IT Professionals and Developers, you will learn to apply cryptographic algorithms to keep your systems safe. First, you will learn the nature of information and see how that understanding directly informs the tools that you choose. Next, you will apply those tools to protect secrets, documents, and systems under your control. Finally, you will explore how to create new tools by coding against cryptographic libraries in C# and Java. When you are finished with this course, you will have the skills and knowledge of cryptography needed to select and apply the correct algorithms to build a complete cryptosystem, and keep your users safe.

