- Course
Discovery with BloodHound
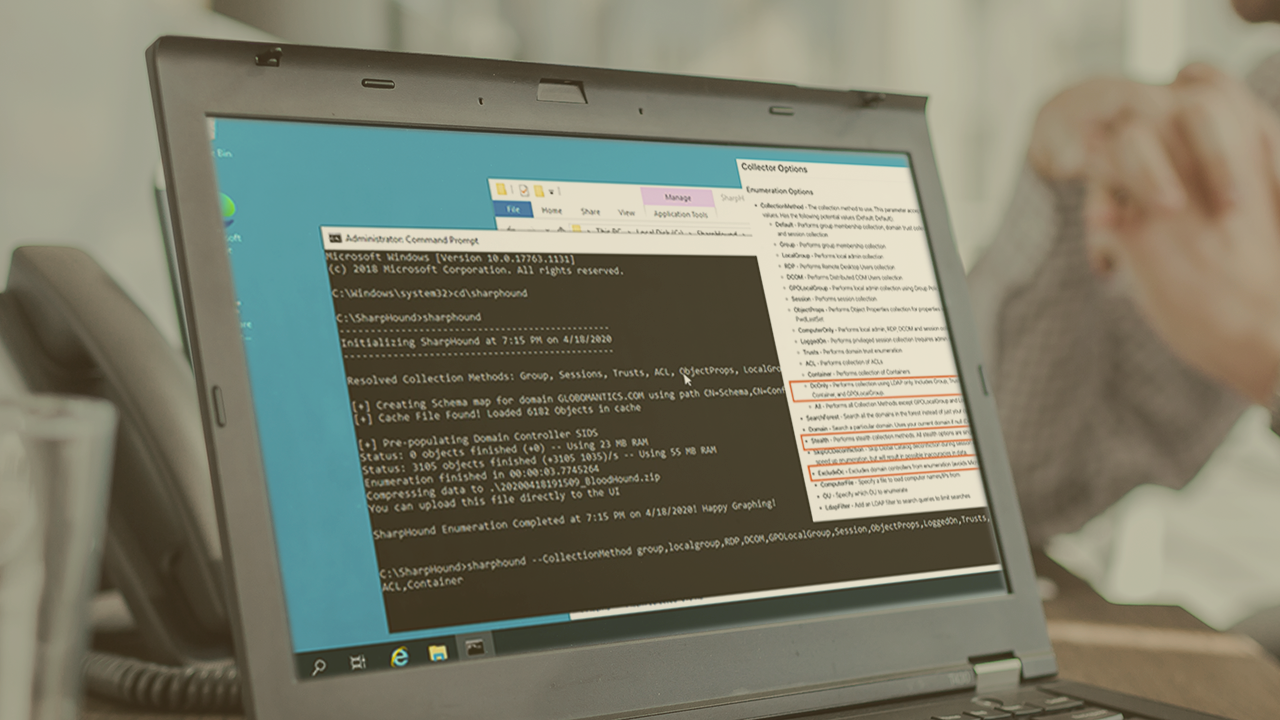
Attacking Active Directory is a great way to achieve control of an environment, letting you access the data, and act on your objectives. BloodHound lets you visualize the shortest path to get to where you need to be.
- Course
Discovery with BloodHound
Attacking Active Directory is a great way to achieve control of an environment, letting you access the data, and act on your objectives. BloodHound lets you visualize the shortest path to get to where you need to be.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Understanding the relationship between thousands of Active Directory objects can be difficult. Users are members of groups, which can be nested in other groups, and linked to thousands of permissions. In this course, Discovery with BloodHound, you will gain the ability to use BloodHound to quickly find the shortest path to compromise systems in an Active Directory environment. First, you will learn how to install BloodHound. Next, you will discover how to use SharpHound to gather data from AD. Finally, you will explore how to ingest and visualize that data, finding paths between objects and the ultimate goal, Domain Admin access. When you are finished with this course, you will have the skills and knowledge of BloodHound needed to start using it to attack AD, or to understand how to better defend it.

