- Course
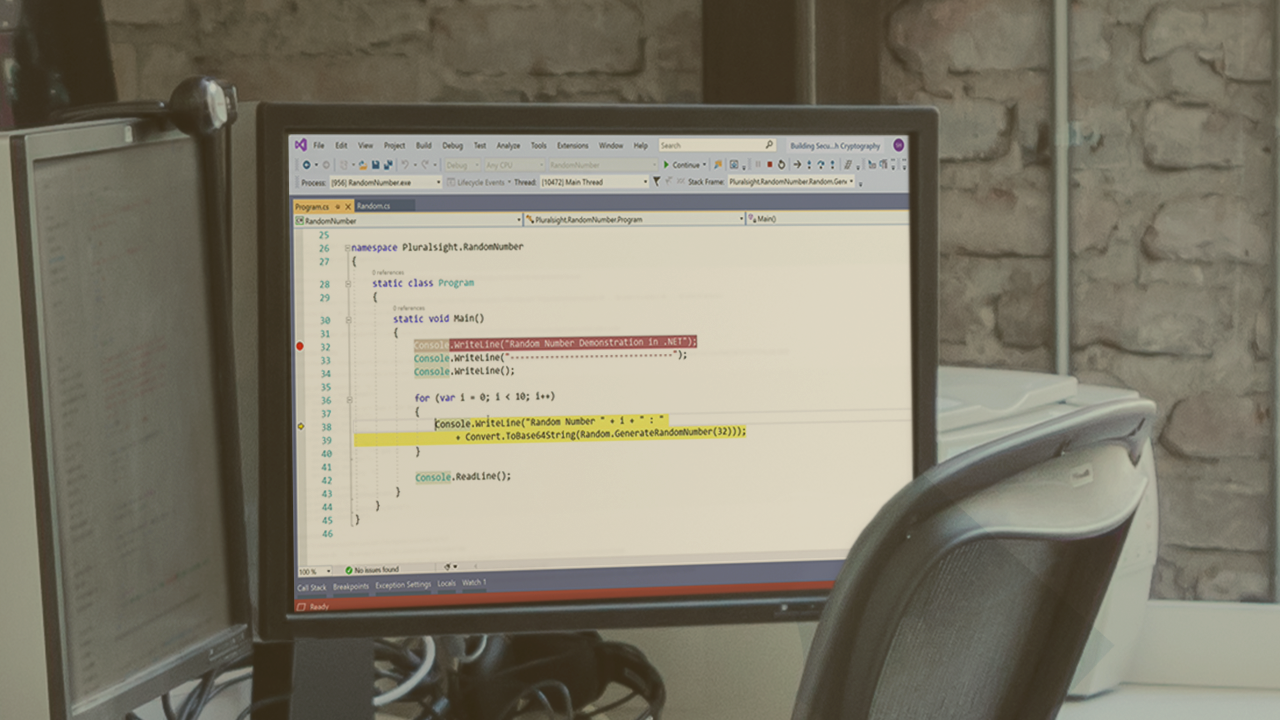
Building Secure Applications with Cryptography in .NET
In this course, you will learn how to use the .NET Framework to protect your data to satisfy confidentiality, integrity, non-repudiation, and authentication.
- Course
Building Secure Applications with Cryptography in .NET
In this course, you will learn how to use the .NET Framework to protect your data to satisfy confidentiality, integrity, non-repudiation, and authentication.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
As a software developer you have a duty to your employer to secure and protect their data. In this course, Building Secure Applications with Cryptography in .NET, you will learn how to use the .NET Base Class Libraries (.NET Framework, .NET Core, .NET 5) to protect your data to satisfy confidentiality, integrity, non-repudiation, and authentication. First, you will explore random number generation and hashing. Then, you will discover authenticated hashing and password based key derivation functions. Finally, you will see both symmetric and asymmetric encryption using AES and RSA. By the end of this course, you will know how to combine these all together to produce a hybrid encryption scheme which includes AES, RSA, HMACS, and Digital Signatures.

