- Course
Analyzing Malware for .NET and Java Binaries
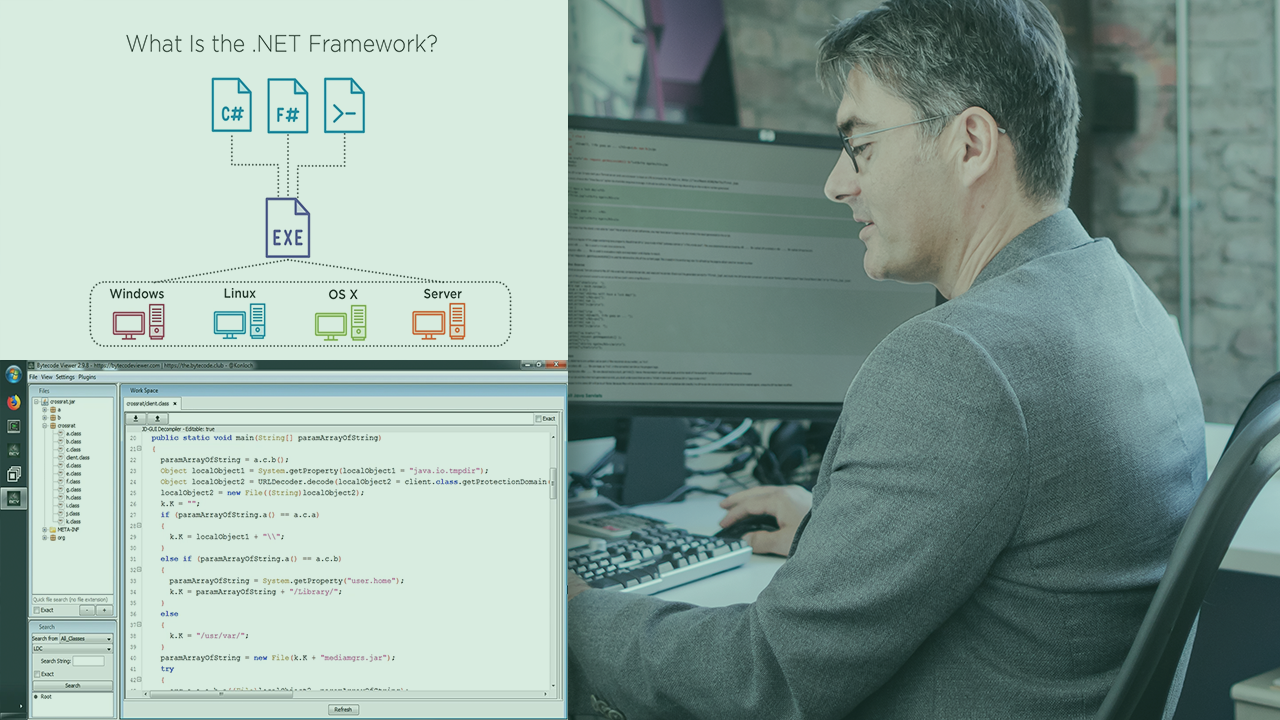
This course will teach the basics of Java and .NET runtimes, introduce tools and techniques for effectively reverse engineering these binary types, show you how to identify indicators of compromise, and get hands-on with real world malware.
- Course
Analyzing Malware for .NET and Java Binaries
This course will teach the basics of Java and .NET runtimes, introduce tools and techniques for effectively reverse engineering these binary types, show you how to identify indicators of compromise, and get hands-on with real world malware.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
The ability to quickly and effectively analyse a wide variety of malware is a critical skill for anyone performing incident response, working in a security operations center (SOC), or analyzing malware. In this course, Analyzing Malware for .NET and Java Binaries, you will gain the skills necessary to effectively analyze Java and .NET malware. First, you will learn how .NET and Java binaries differ from other malware. Next, you will learn the tools, techniques, and workflows necessary to reverse engineer these types of binaries. Finally, you will apply everything you learned through hands-on labs in which you will analyze real-world malware. When you are finished with this course, you will have the knowledge and skills necessary to analyze .NET and Java binaries, giving you the ability to effectively investigate a wider variety of malware.

