- Course
How to Stop Man-in-the-Middle and Downgrade Attacks in Your Apps
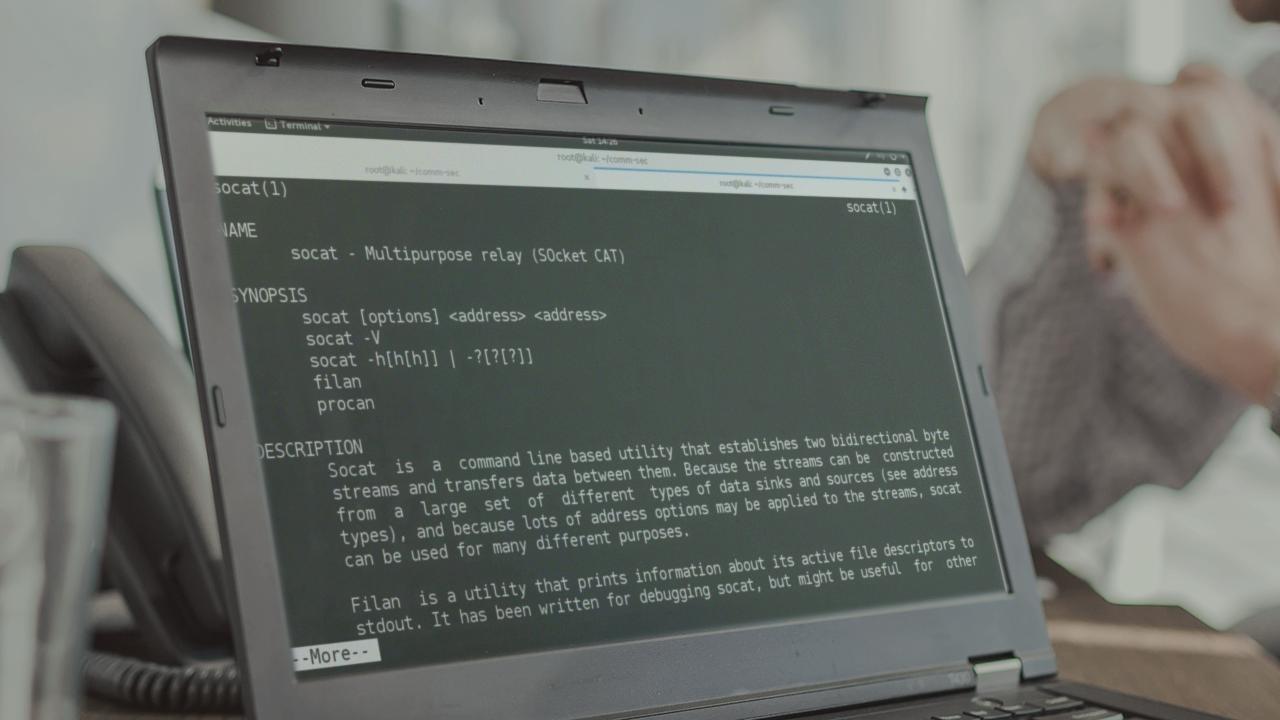
Securing communications over untrusted networks is a critical element of security for any modern application. In this course, you will learn how to simulate man-in-the-middle attacks to test for these problems, and learn how to prevent them.
- Course
How to Stop Man-in-the-Middle and Downgrade Attacks in Your Apps
Securing communications over untrusted networks is a critical element of security for any modern application. In this course, you will learn how to simulate man-in-the-middle attacks to test for these problems, and learn how to prevent them.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
While one of the cornerstones of application security is securing communications over untrusted networks, far too often developers and operations personnel get tripped up by the many pitfalls of implementation, often resulting in the complete failure to secure data on the wire. In this course, you'll learn how adversaries can gain access to other users' communications through a variety of techniques, and prevention strategies. The course covers specific topics ranging from the SSL/TLS certificate authority system, to secure web session management and mobile communications security. You'll also learn how to conduct simulated man-in-the-middle attacks to empirically test SSL/TLS certificate validation in realistic scenarios. By the end of this course, you'll have a thorough understanding of techniques to prevent interception and make applications more secure.

