- Course
Enumerating the Network Infrastructure as a Forensics Analyst
This course will teach you how to apply your theoretical knowledge of networking to both real time and post incident forensic analysis of network based data.
- Course
Enumerating the Network Infrastructure as a Forensics Analyst
This course will teach you how to apply your theoretical knowledge of networking to both real time and post incident forensic analysis of network based data.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
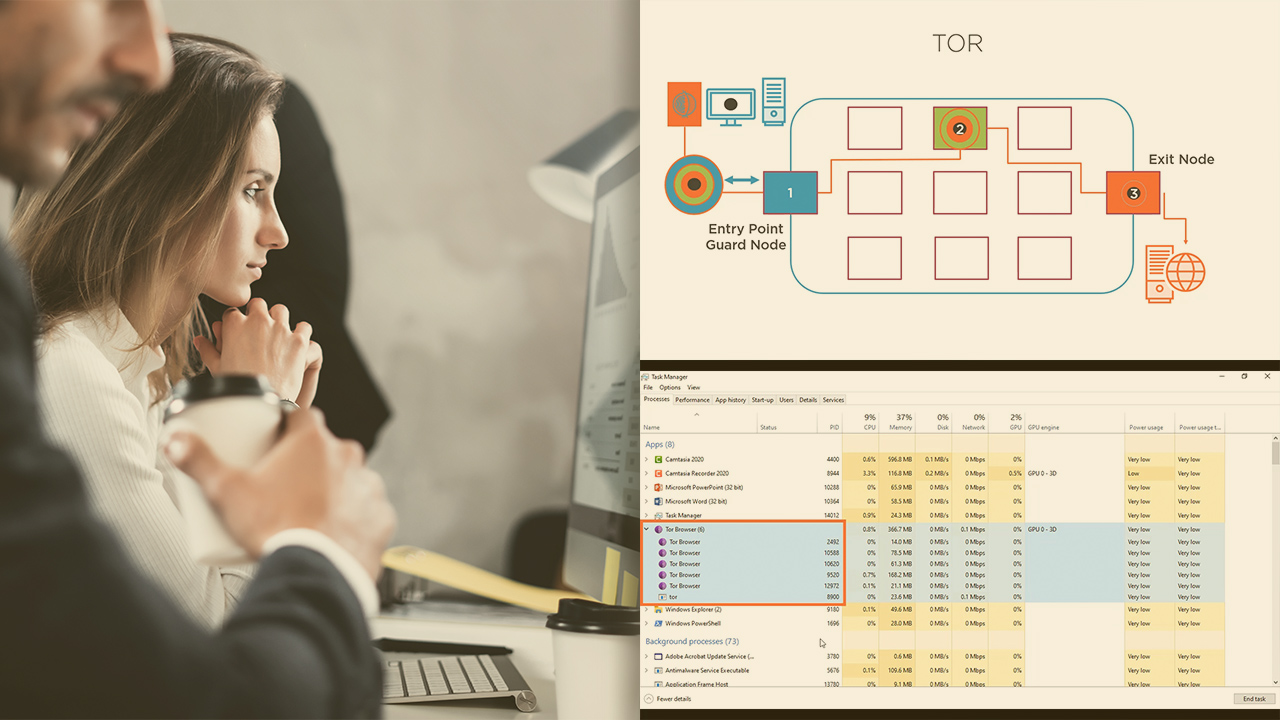
Cyber crimes are a continual threat to any network, and having a strategy to prevent, protect and pursue is increasingly important. In this course, Enumerating the Network Infrastructure as a Forensics Analyst, you’ll learn how to apply the theoretical knowledge of TCP/IP and network-based protocols and devices to assist in the collection, analysis, and dissemination of network-based material and evidence as part of a forensic investigation. First, you’ll explore the key elements of TCP/IP and how they apply within the world of forensic investigation. Next, you’ll discover how your knowledge of physical and logical networking can assist you in finding material quickly and efficiently. Finally, you’ll learn how to analyze network-based data and material to draw confident conclusions to events and incidents which may have occurred. When you’re finished with this course, you’ll have the skills and knowledge of enumerating the network infrastructure needed to collect, collate, and forensically analyze material from a wide range of sources which will assist you in producing evidential reports, fast time support to interview and supporting ongoing investigation.

