- Course
Ethical Hacking: Cryptography
The Internet is an insecure medium, and attackers can see a lot of what you are sending. This is where cryptography comes in to play. Looking at cryptography from the attackers point a view is the best way to start protecting your resources.
- Course
Ethical Hacking: Cryptography
The Internet is an insecure medium, and attackers can see a lot of what you are sending. This is where cryptography comes in to play. Looking at cryptography from the attackers point a view is the best way to start protecting your resources.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Today the Internet is a part of our everyday life’s. From work to home, we are using the Internet for sending data back and forth across this public network. Some information is just a request for a webpage, while other requests are extremely confidential; like passwords, medical data, or financial data. Cryptography is the technology that we can use to changing the plain text to unreadable text. We use it during authentication, as well as to transfer data and to keep data confidential.
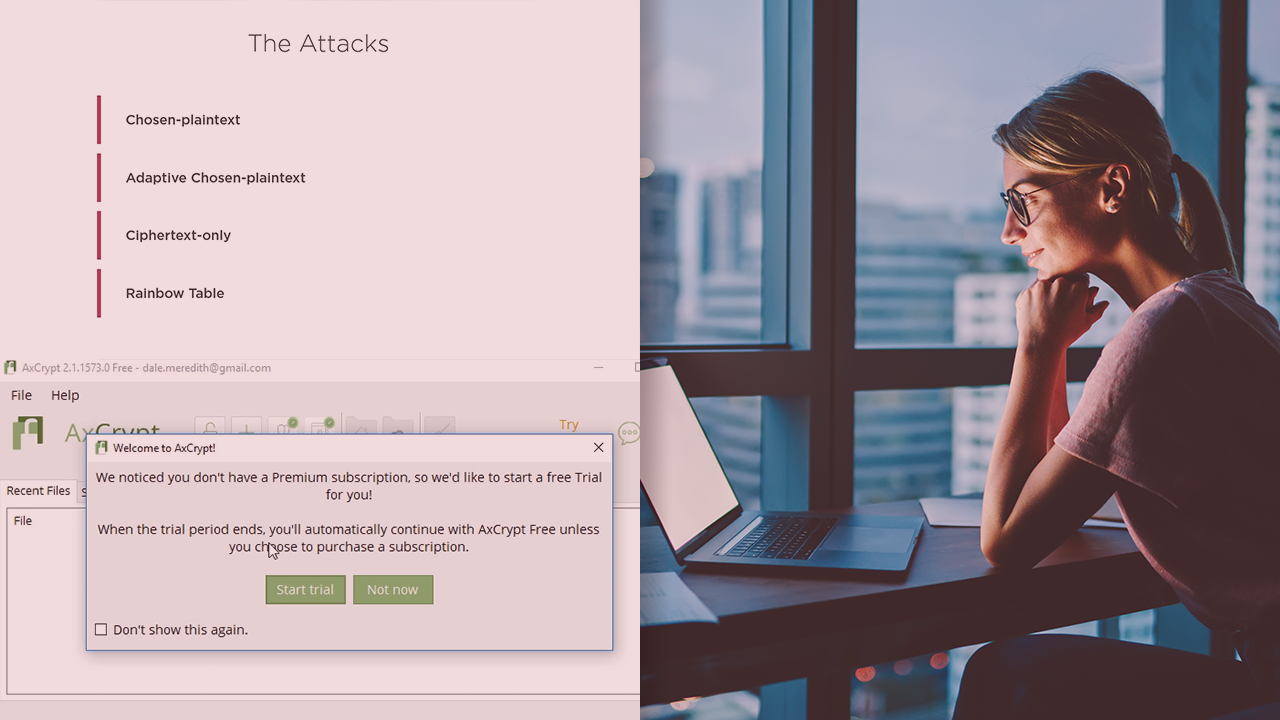
In this course, Ethical Hacking: Cryptography, you’ll learn the overall concepts of cryptography. First, you'll explore the different algorithms used along with those key concepts. Next, you’ll find out about the different tools and apps for both PC’s and mobile devices that you can use to deploy different types of cryptography. Finally, you’ll dive into what attacks might be thrown at you by attackers and how to protect yourself and your resources. By the end of this course, you'll gain greater knowledge of cryptography and how you can better implement it for your organization.

