- Course
Execution with Donut
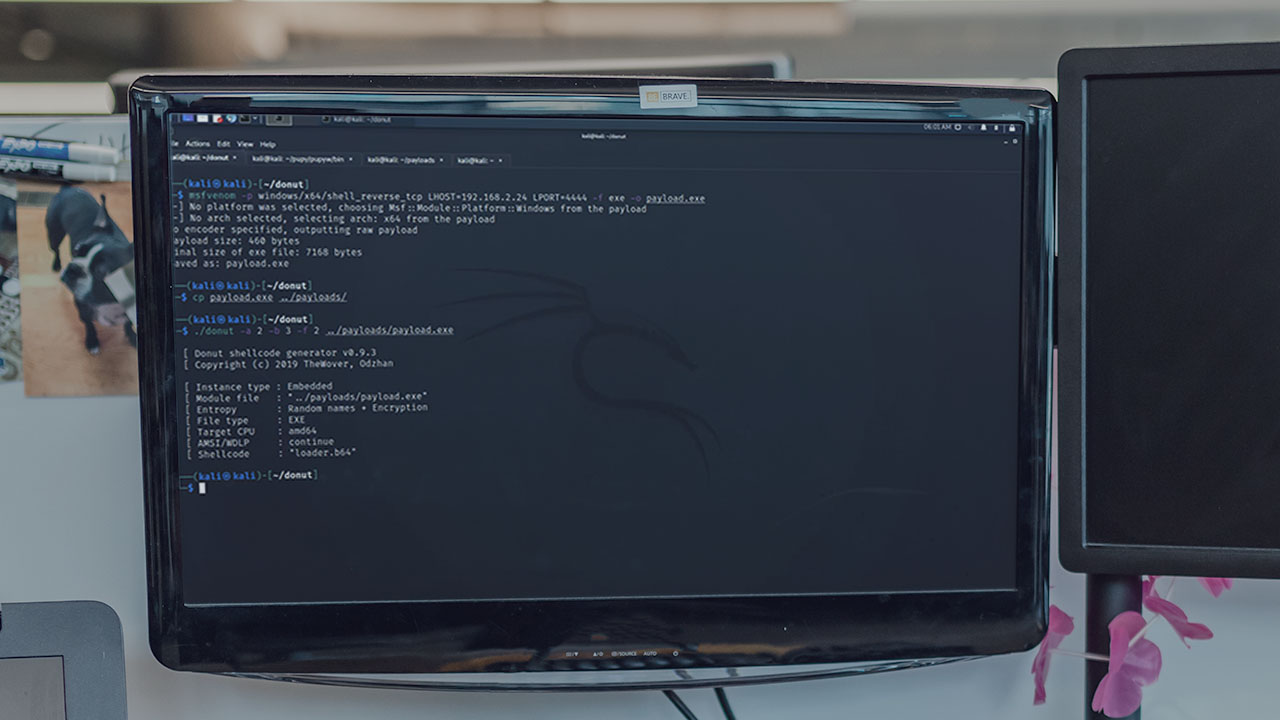
In this course you will learn execution and defense evasion using Donut.
- Course
Execution with Donut
In this course you will learn execution and defense evasion using Donut.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Are you looking for a tool to generate shellcode for use on Windows machines? In this course, Execution with Donut, you'll learn how to utilize Donut to execute malicious code in a red team environment. First, you'll see how to use Donut to generate shellcode from an executable. Next, you'll explore this technique to generate shellcode from a common C2 application. Finally, you'll learn defense evasion techniques by executing the shellcode on a remote host. When you're finished with this course, you'll have the skills and knowledge to execute these techniques: Native API - ID: T1106, Portable Executable Injection – ID: T1055.002, and Dynamic-link Library Injection – ID: T1055.001. Knowing how these techniques can be used against you will ultimately lend to your ability as an organization, or an individual, to detect and defend against specific attack vectors.

