- Course
Getting Started with Endpoint Log Analysis
In this course on machine data, you will explore the details of the data that our electronic devices generate. This will be through the use of analysis techniques that will hone your skills to identify malicious activity in a simulated enterprise.
- Course
Getting Started with Endpoint Log Analysis
In this course on machine data, you will explore the details of the data that our electronic devices generate. This will be through the use of analysis techniques that will hone your skills to identify malicious activity in a simulated enterprise.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
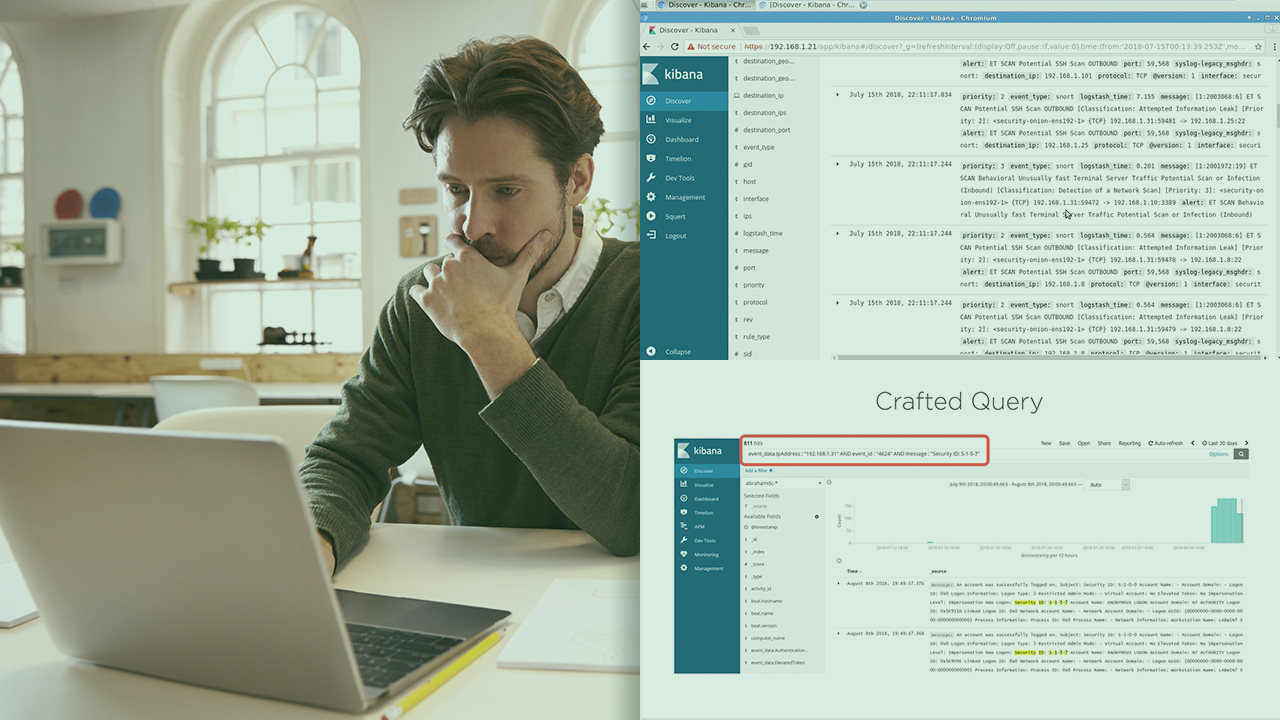
In today’s cybersecurity landscape, the threats are everywhere. Our environments can be compromised from too many attack vectors, both from inside of our network and outside of it. This makes monitoring operations extremely difficult to keep up with. As we include more and more technology within our infrastructure, the amount of machine data that we generate increases as well, and it’s this data that will help us determine malicious activity. In this course, Getting Started with Endpoint Log Analysis, you will learn the skills needed to be able to parse and analyze machine data. First, you will explore what machine data is. Next, you will learn how to inspect machine data, and recognize recon activity. Finally, you will discover how to analyze and search machine data, as well as learn to use machine data to track attacker activity. When you are finished with this course, you will have foundational knowledge about machine data and be able to assist in the continuous monitoring operations within your environment.

