- Course
Getting Started with osquery
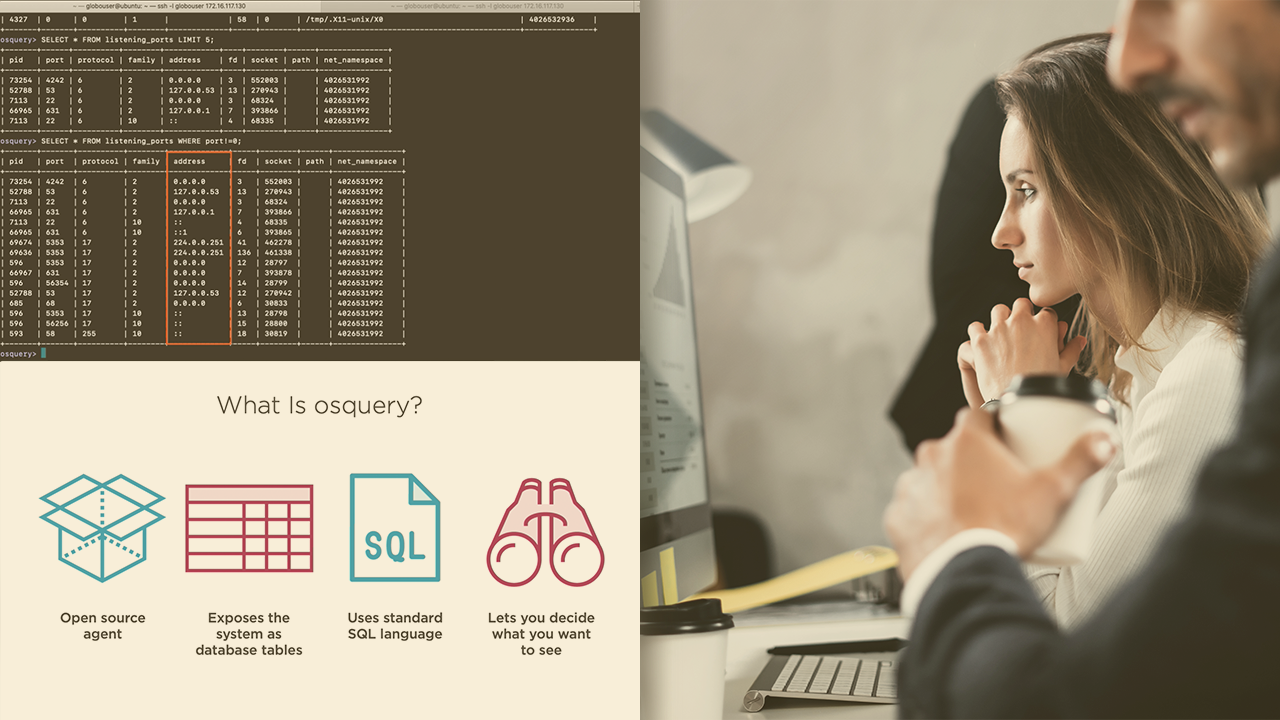
Learn how to deploy, configure, and use osquery to improve security by increasing visibility, detecting suspicious activity, and implementing features like File Integrity Monitoring, using this great cross-platform tool.
- Course
Getting Started with osquery
Learn how to deploy, configure, and use osquery to improve security by increasing visibility, detecting suspicious activity, and implementing features like File Integrity Monitoring, using this great cross-platform tool.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Understanding how to leverage the power of osquery to solve security problems can seem complicated.
In this course, Getting Started with osquery, you will gain the ability to not only install and configure osquery, but also to understand different aspects of using it in a real environment.
First, you"ll learn how to install it on Linux and Windows.
Next, you'll discover how the power of SQL can be used with it to solve security problems, like identifying what processes are being executed where, and real-time events will be leveraged so you can learn how to monitor activity between scheduled query intervals and implement File Integrity Monitoring.
Finally, you'll explore how to plan for a real deployment of osquery, including the use of advanced options like TLS logging and extensions.
When you're finished with this course, you'll have the skills and knowledge of osquery needed to plan a deployment and start writing queries that will help you get answers to your most important endpoint security questions.
Software required: a Linux (Ubuntu, Debian, Redhat or CentOS) system with the latest version of osquery stable.

