- Course
Group Policy: Advanced Targeting
Active Directory Group Policy is a powerful tool; however, many people don't realize its full potential. In this course, you'll learn how to use Active Directory to target complex edge cases as well as to replace manual tasks or logon scripts.
- Course
Group Policy: Advanced Targeting
Active Directory Group Policy is a powerful tool; however, many people don't realize its full potential. In this course, you'll learn how to use Active Directory to target complex edge cases as well as to replace manual tasks or logon scripts.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
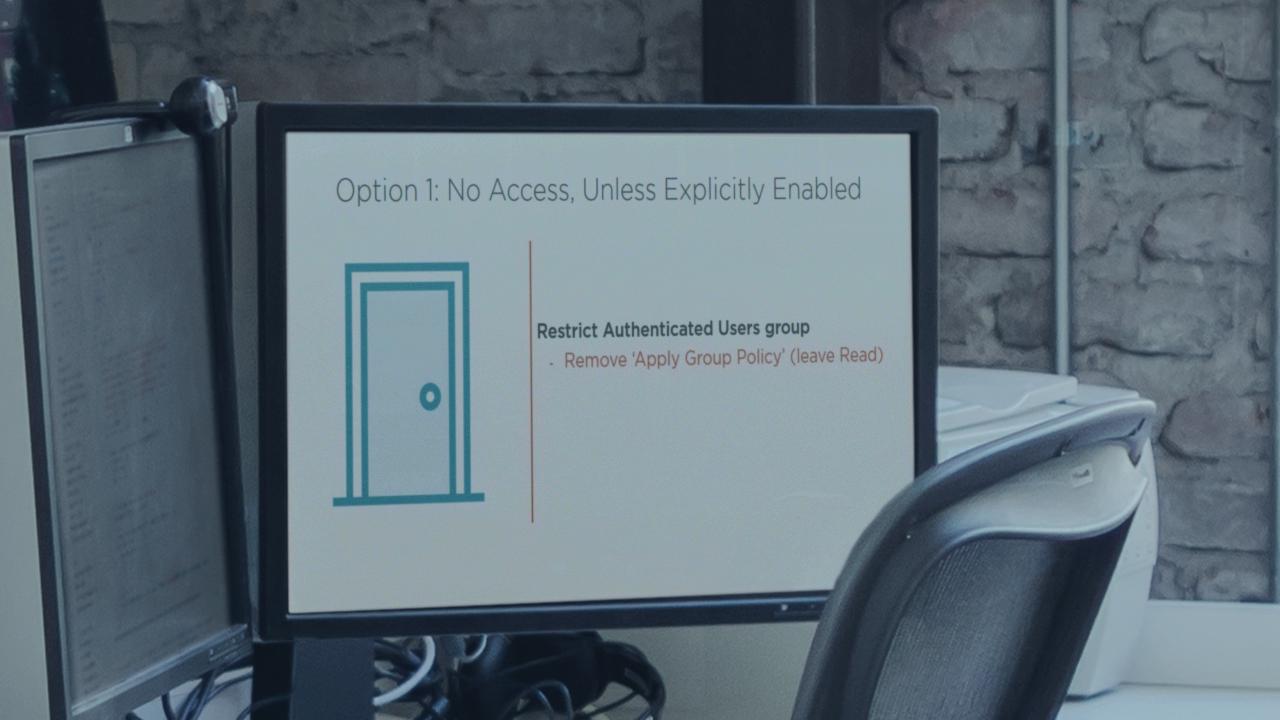
If you thought GPO settings can only be applied by linking GPOs to OUs, then you've just barely touched the surface. In this course, Group Policy: Advanced Targeting, you will learn how to get the most out of group policy and this course may also enlighten you to features you didn't know existed. First, you'll learn how to control Group Policy settings using security groups rather than the GPMC. Next, you'll be walked through the end-to-end process for dynamic WMI filtering, as well as shown tools to help you decipher the WMI query language. Finally, you'll be shown how to replace logon scripts and other manual tasks quickly and easily by using Item Level Targeting and Group Policy Preferences. By the end of this course, you'll know how to address almost any edge case and understand how to replace your legacy logon scripts.

