- Course
Hack Yourself First: How to go on the Cyber-Offense
"Hack Yourself First" is all about developers building up cyber-offense skills and proactively seeking out security vulnerabilities in their own websites before an attacker does.
- Course
Hack Yourself First: How to go on the Cyber-Offense
"Hack Yourself First" is all about developers building up cyber-offense skills and proactively seeking out security vulnerabilities in their own websites before an attacker does.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
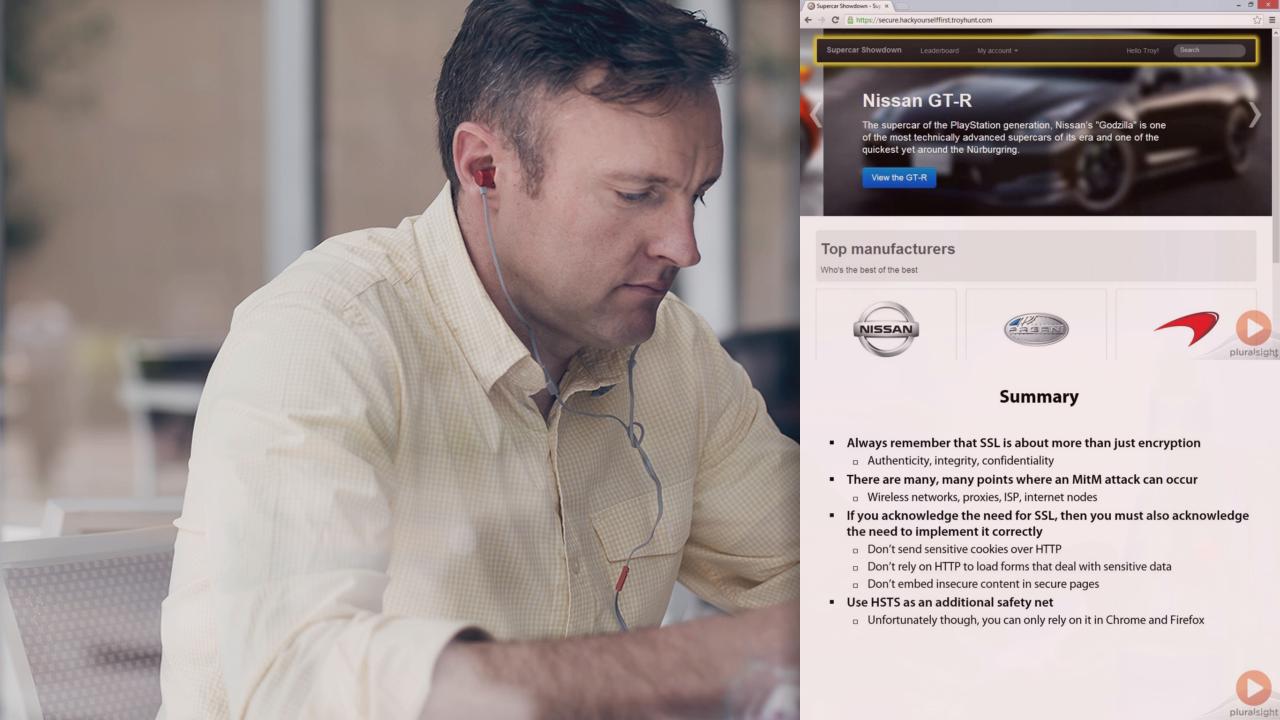
The prevalence of online attacks against websites has accelerated quickly in recent years and the same risks continue to be readily exploited. However, these are very often easily identified directly within the browser; it's just a matter of understanding the vulnerable patterns to look for. This course comes at security from the view of the attacker in that their entry point is typically the browser. They have a website they want to probe for security risks – this is how they go about it. This approach is more reflective of the real online threat than reviewing source code is and it empowers developers to begin immediately assessing their applications even when they're running in a live environment without access to the source. After all, that's what online attackers are doing.
Hack Yourself First: How to go on the Cyber-Offense
-
Introduction | 1m 31s
-
The three objectives of transport layer protection | 3m
-
Understanding a man in the middle attack | 3m 53s
-
Protecting sensitive data in transit | 6m 24s
-
The risk of sending cookies over insecure connections | 12m 57s
-
How loading login forms over HTTP is risky | 19m 29s
-
Exploiting mixed-mode content | 10m 39s
-
The HSTS header | 7m 11s
-
Summary | 3m 5s

