- Course
Identity and Access Control in ASP.NET 4.5
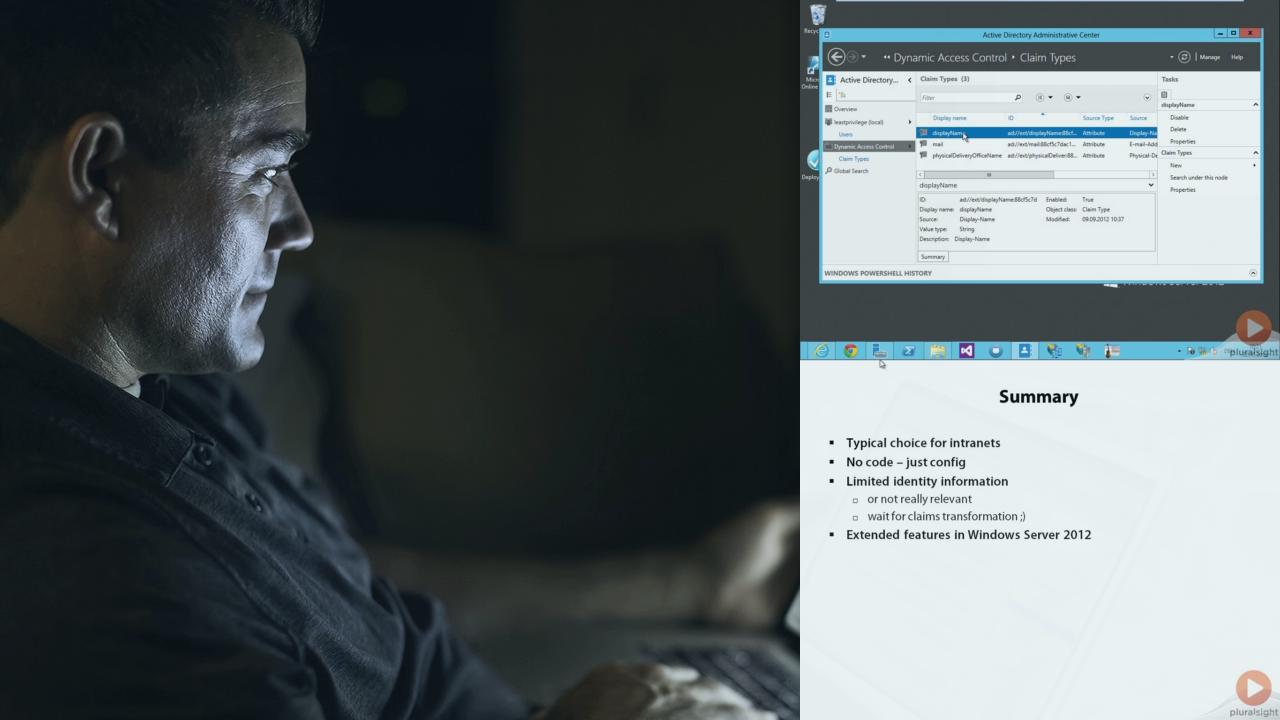
Implementing claims-based identity, federation, authentication & authorization in ASP.NET 4.5
- Course
Identity and Access Control in ASP.NET 4.5
Implementing claims-based identity, federation, authentication & authorization in ASP.NET 4.5
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
If you need to implement authentication and authorization in an ASP.NET application, this course is for you. Authentication mechanisms are explored in detail, including Windows, Forms, and federated authentication. This course also examines how to work with .NET 4.5's claims-based identity and authorization, as well as patterns such as single sign-on/out, federation and home realm discovery.

