- Course
Identity and Access Control in WCF 4.5
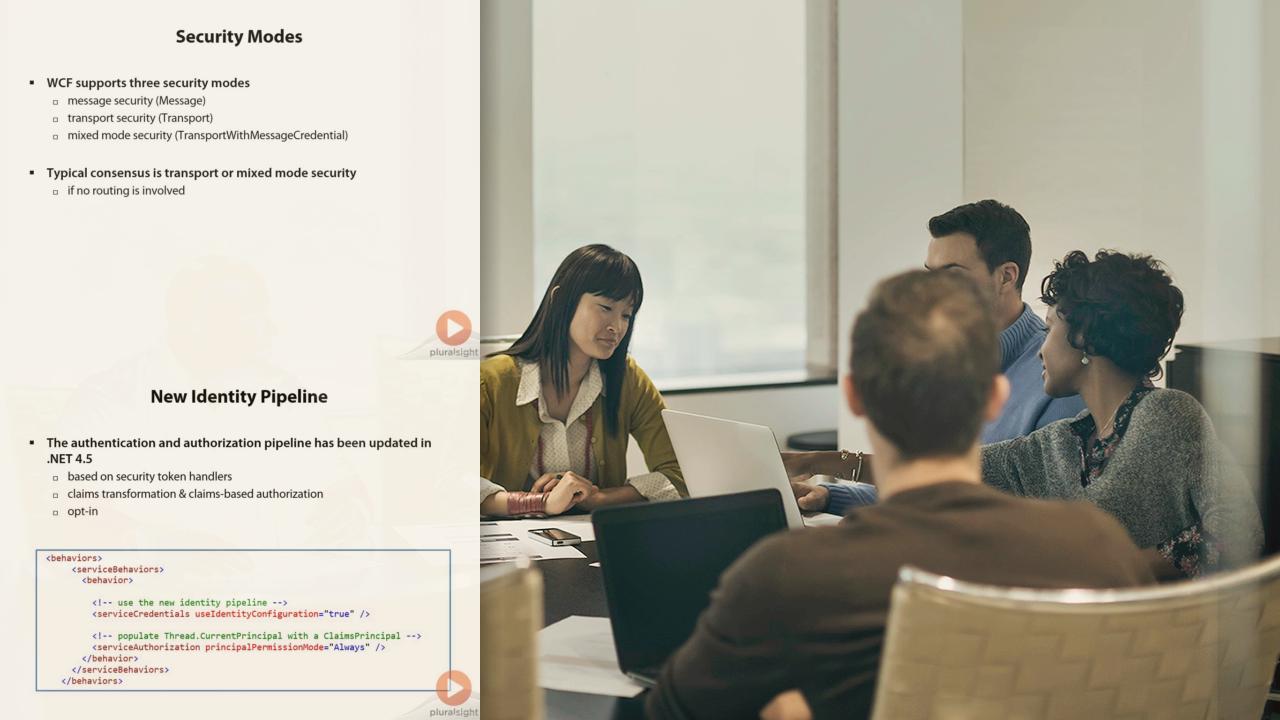
Implementing claims-based identity, federation, authentication and authorization in WCF 4.5.
- Course
Identity and Access Control in WCF 4.5
Implementing claims-based identity, federation, authentication and authorization in WCF 4.5.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
If you need to implement authentication and authorization in a WCF service, this course is for you. Topics covered include how to use Windows, UserName and WS-Trust authentication, as well as how to work with claims-based identity and authorization. This course also presents patterns such as federation and identity delegation.

