- Course
Identity and Access Management on AWS: Roles and Groups
This course explains the proper use of roles and groups in AWS and provides best practices for their use. It also covers the tools that can be used to audit the use of IAM.
- Course
Identity and Access Management on AWS: Roles and Groups
This course explains the proper use of roles and groups in AWS and provides best practices for their use. It also covers the tools that can be used to audit the use of IAM.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
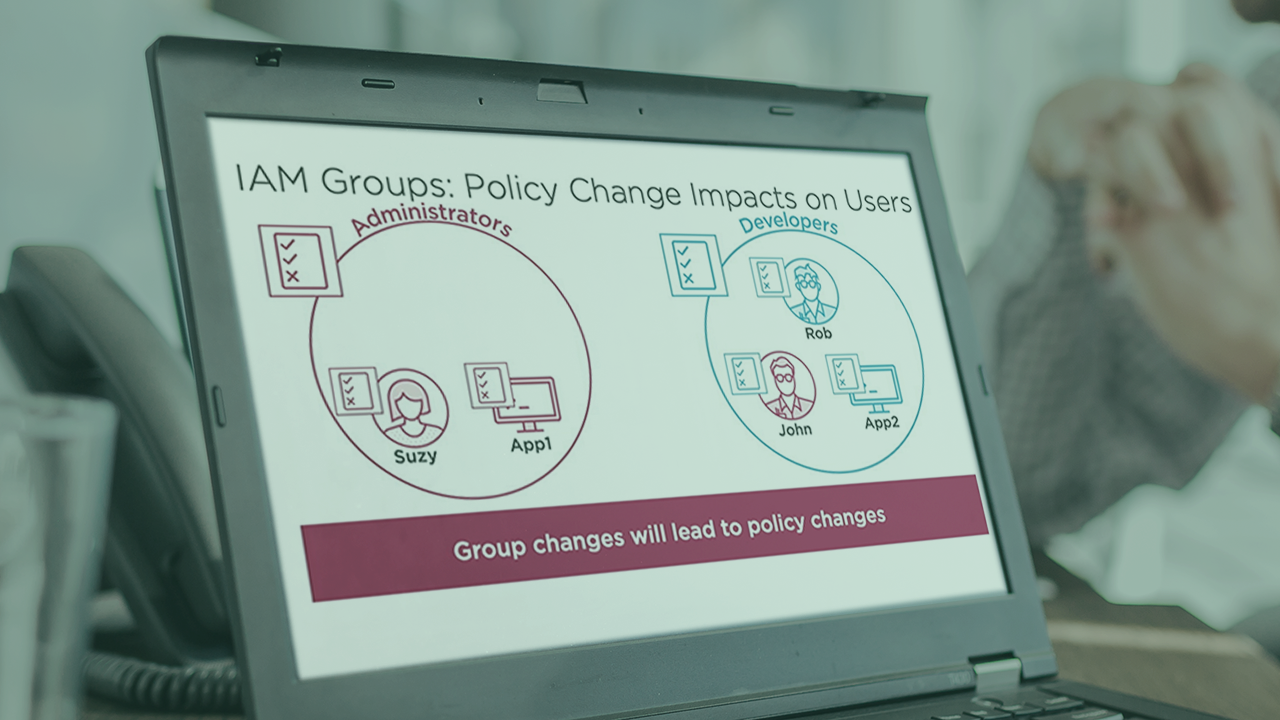
Using individual users for all access control is fine for small companies, but when you have tens, hundreds, thousands, or more users and interactions with other companies, this doesn’t scale well. Additionally, auditing the use of the various users, groups, and roles is critical to organizations of all sizes. In this course, Identity and Access Management on AWS: Roles and Groups, you will gain the ability to manage organizations of any size and to use roles properly. You'll also learn how to describe the various tools that are available to audit and manage the use of IAM. First, you will examine how groups can be used to simplify the management of collections of users. Next, you will discover the various use cases for roles, including some of the types of roles that help in those use cases. The role of the Security Token Service (STS) in relation to roles will be discussed. Best practices in relation to roles is also an important topic to be considered, as roles are one of the most misunderstood things in all of IAM. Finally, you will discover how to use the various tools that Amazon provides to manage, optimize, and audit IAM and the use of IAM permissions, including Credential Report, Access Advisor, CloudTrail, Trusted Advisor, and AWS Config. When you’re finished with this course, you will have the skills and knowledge to use roles and groups to secure your AWS infrastructure and to audit and optimize usage of IAM in AWS.
Identity and Access Management on AWS: Roles and Groups
-
Course Introduction | 1m 38s
-
IAM Users and Policies Overview | 3m 12s
-
AWS CloudTrail | 4m 23s
-
Demo 1: Configure AWS CloudTrail | 4m 3s
-
IAM Groups | 3m 15s
-
Demo 2: IAM Groups | 5m 21s
-
Policy Changes | 2m 1s
-
Multiple Policies | 54s
-
Group Scenario | 6m 12s
-
Demo 3: Managing IAM Users in IAM Groups | 6m 31s
-
Best Practices | 57s
-
Summary | 1m 10s

