- Course
Introduction to IIS Certificates
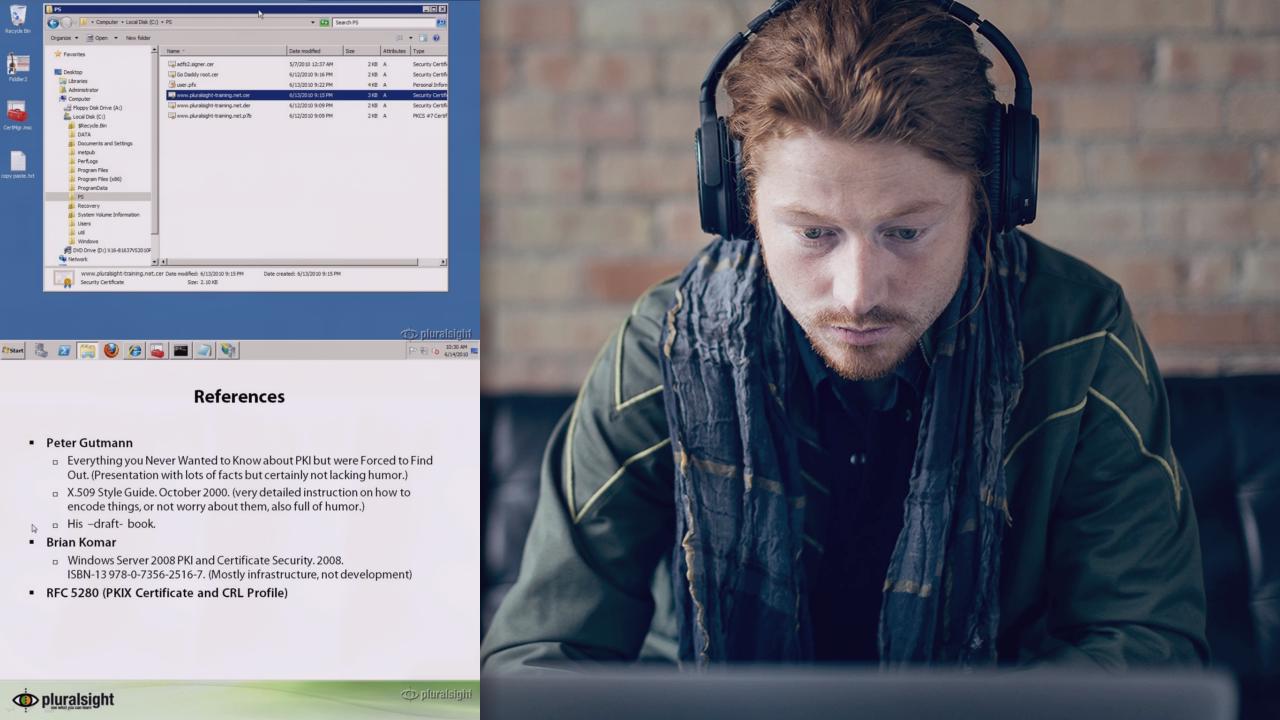
Describes encryption keys, how they are bound to a Subject name in a certificate, tools to deal with certificates and Certificate authorities
- Course
Introduction to IIS Certificates
Describes encryption keys, how they are bound to a Subject name in a certificate, tools to deal with certificates and Certificate authorities
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Developers have to deal with certificates quite often. The are used by WEB servers and Web browsers, used to sign documents etc. This course introduces the practical aspects of public key cryptography. It shows the layout of certificates, the tools to manipulate them, how to obtain them, do key maintenance. Briefly touches on self signed certificates. Describes CA hierarchies and shows the Chain Building process. References to further literature.

