- Course
Implementing the 20 CIS Critical Security Controls
Securing company information is a significant responsibility that can be stressful and overwhelming, but you're not alone. This course will provide you with a comprehensive but digestible framework to confront a majority of infosec risks.
- Course
Implementing the 20 CIS Critical Security Controls
Securing company information is a significant responsibility that can be stressful and overwhelming, but you're not alone. This course will provide you with a comprehensive but digestible framework to confront a majority of infosec risks.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
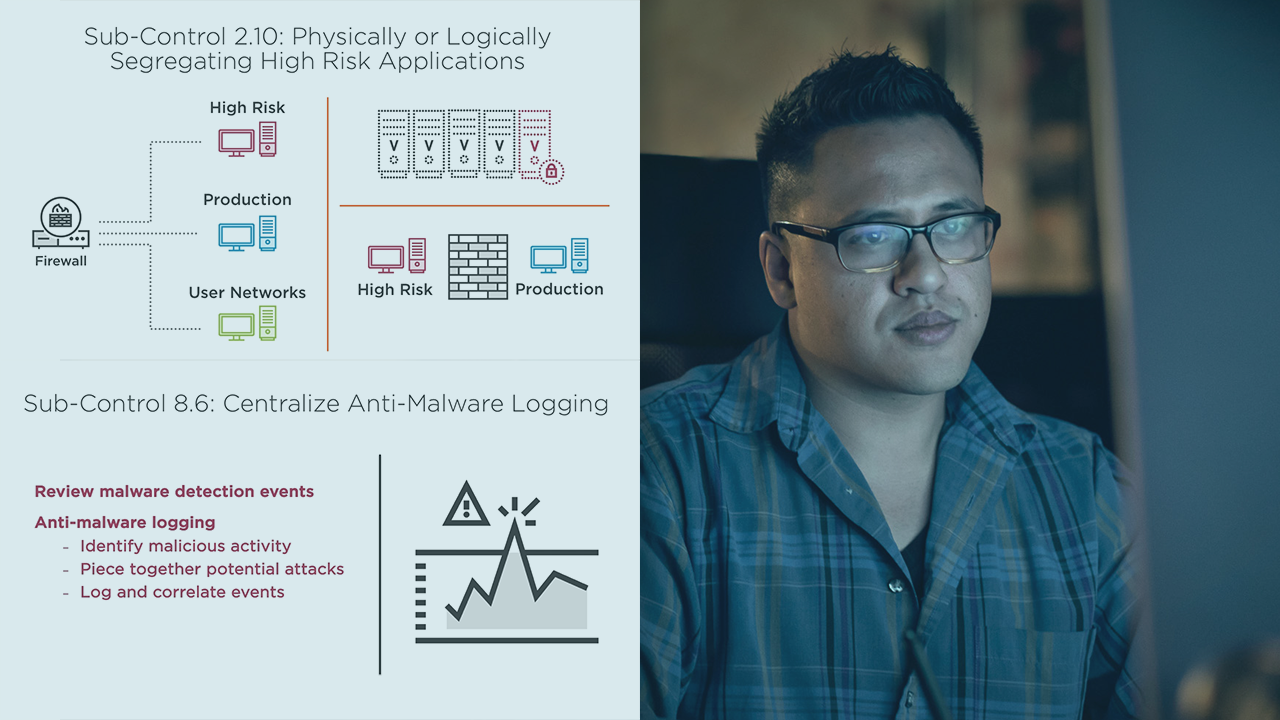
A question familiar to every information security professional is, “where do I start?” The CIS Controls get to the heart of the information security problem, putting security professionals in a position to make immediate and meaningful progress early in an information security program. In this course, Implementing the 20 CIS Critical Security Controls, you will find a practical framework to manage information security risks. First, you will learn about the history and purpose of the CIS controls. Next, you will learn about implementation groups to better understand the controls and sub-controls that make sense for your organization to implement. Finally, you will be equipped with 20 controls and over 170 sub-controls that can be customized to meet your organization's unique security requirements. When you're finished with this course, you will have the fundamental knowledge to address a majority of information security risks in your organization.

