- Course
Incident Forensics: Digital Media Acquisition
The first step on a forensic investigation is to acquire the data related to the incident. In this course, you will learn how to acquire data from devices (such as laptops, hard drives and USB sticks) following a proper forensic methodology.
- Course
Incident Forensics: Digital Media Acquisition
The first step on a forensic investigation is to acquire the data related to the incident. In this course, you will learn how to acquire data from devices (such as laptops, hard drives and USB sticks) following a proper forensic methodology.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
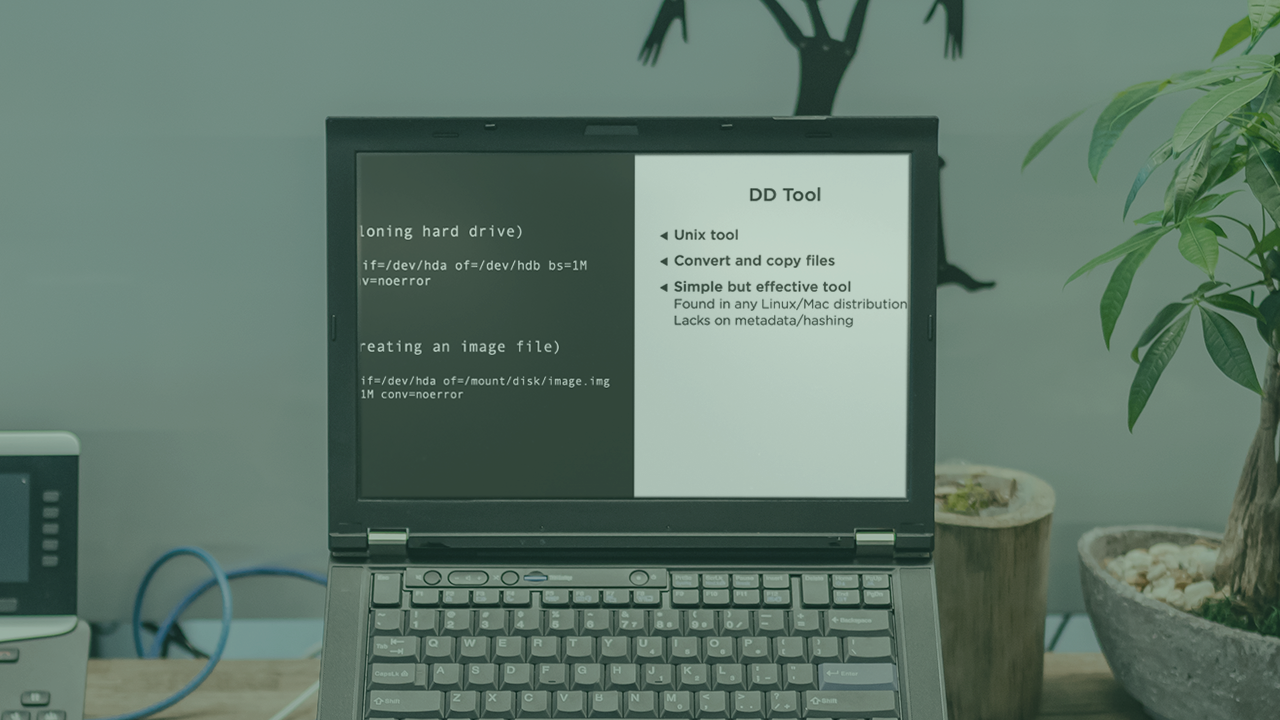
The acquisition of digital media (such as laptops, hard drives, and USB sticks) is the first step in a cyber forensic case. The acquisition should be conducted in such a way that all the pieces of evidence are reliable enough to be presented in court if necessary. In this course, Incident Forensics: Digital Media Acquisition, we cover every single step of a digital media acquisition, including not only the technical part but also the overall forensic methodology that should be followed. First, you will be presented with some vital forensic concepts, such as chain of custody. Next, you will explore all the pre-requisites before the data acquisition. After, we show through demos how to image the most common digital media types using a professional forensic methodology. Finally, you will discover how to organize all of the evidence and create work copies for the forensic investigators. All the forensic acquisition task follows strict processes and procedures that ensure that the data will not be tampered with and the evidence is reliable. Throughout the course, you will follow a real-world scenario in which an employee was selling confidential information to competitors. By the end of this course, you will be prepared and have the knowledge to be the forensic technician responsible for acquiring the data related to any case.

