- Course
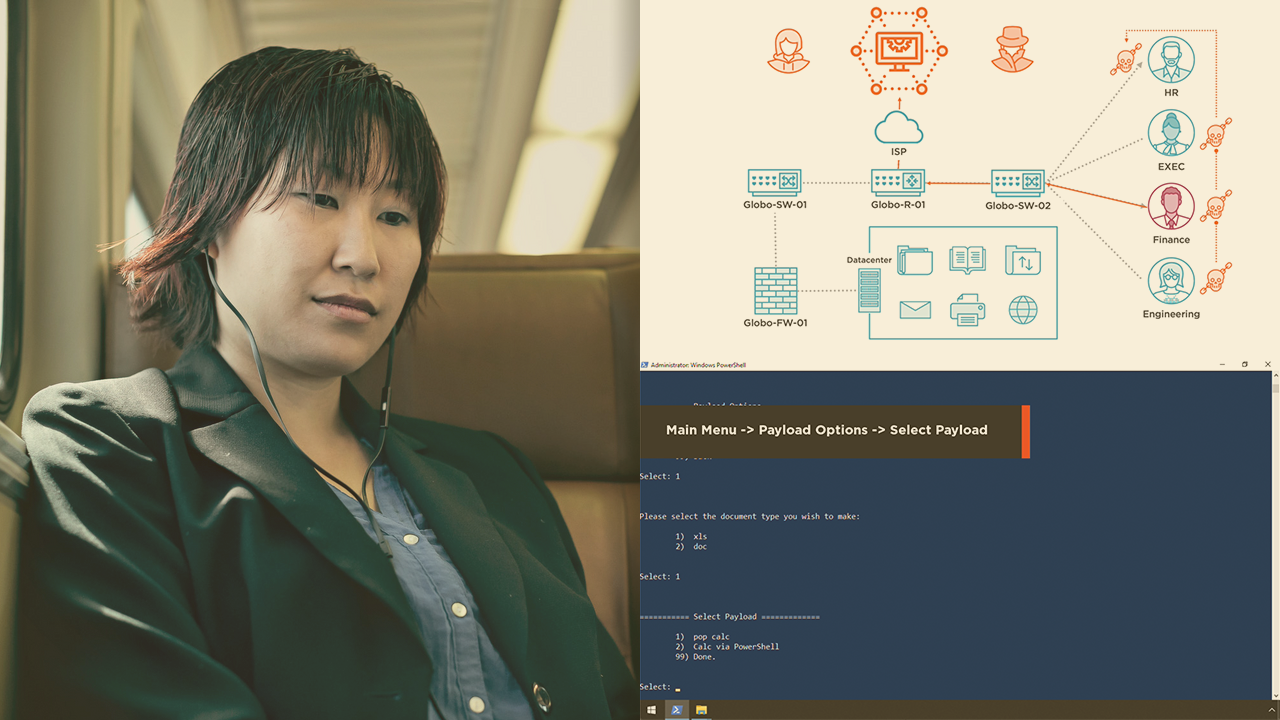
Initial Access with Luckystrike
Malicious office documents are an effective way to gain an initial foothold into a network. In this course, you will learn how to use Luckystrike to create custom malicious office documents, manage multiple payloads, and utilize custom templates.
- Course
Initial Access with Luckystrike
Malicious office documents are an effective way to gain an initial foothold into a network. In this course, you will learn how to use Luckystrike to create custom malicious office documents, manage multiple payloads, and utilize custom templates.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Creating and managing malicious office documents is a common red team task. However, it can become very tedious managing all of the payloads, templates, and potential anti-virus bypasses. In this course, Initial Access with Luckystrike, you will gain the ability to not only create malicious office documents, but manage them in a straight-forward framework. First, you will learn how to build your catalog to add a variety of payloads. Next, you will discover how to import templates to help create custom malicious office documents. Finally, you will explore how integrate custom payloads from other red team tools. When you are finished with this course, you will have the skills and knowledge of Luckystrike needed to manage all of your malicious document needs.

