- Course
Exploitation with Kali Linux
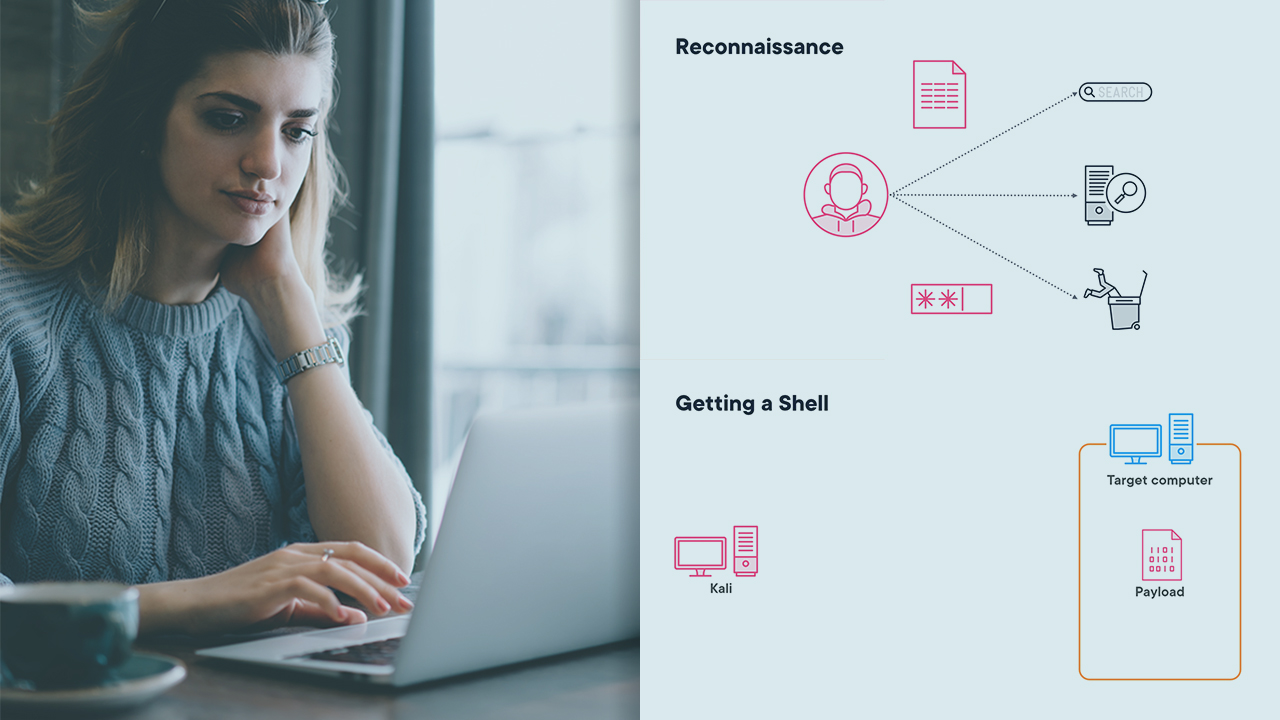
Kali contains an array of tools to assist with security assessments and penetration tests. This course will teach you how to use some of those tools to exploit the systems you find, moving you into a position to perform post exploitation tasks.
- Course
Exploitation with Kali Linux
Kali contains an array of tools to assist with security assessments and penetration tests. This course will teach you how to use some of those tools to exploit the systems you find, moving you into a position to perform post exploitation tasks.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
A large number of security tools are available to help with a penetration test and understanding how to use them is critical to make testing effective. In this course, Exploitation with Kali Linux, you’ll learn to exploit the vulnerabilities you find. First, you’ll learn how to access systems using CrackMapExec. Next, you’ll discover how to create and use payloads to initially exploit a computer. Finally, you’ll learn how to use Metasploit alone to exploit remote systems and prepare for post exploitation. When you’re finished with this course, you’ll have the skills and knowledge to comfortably exploit computers within a network.

