- Course
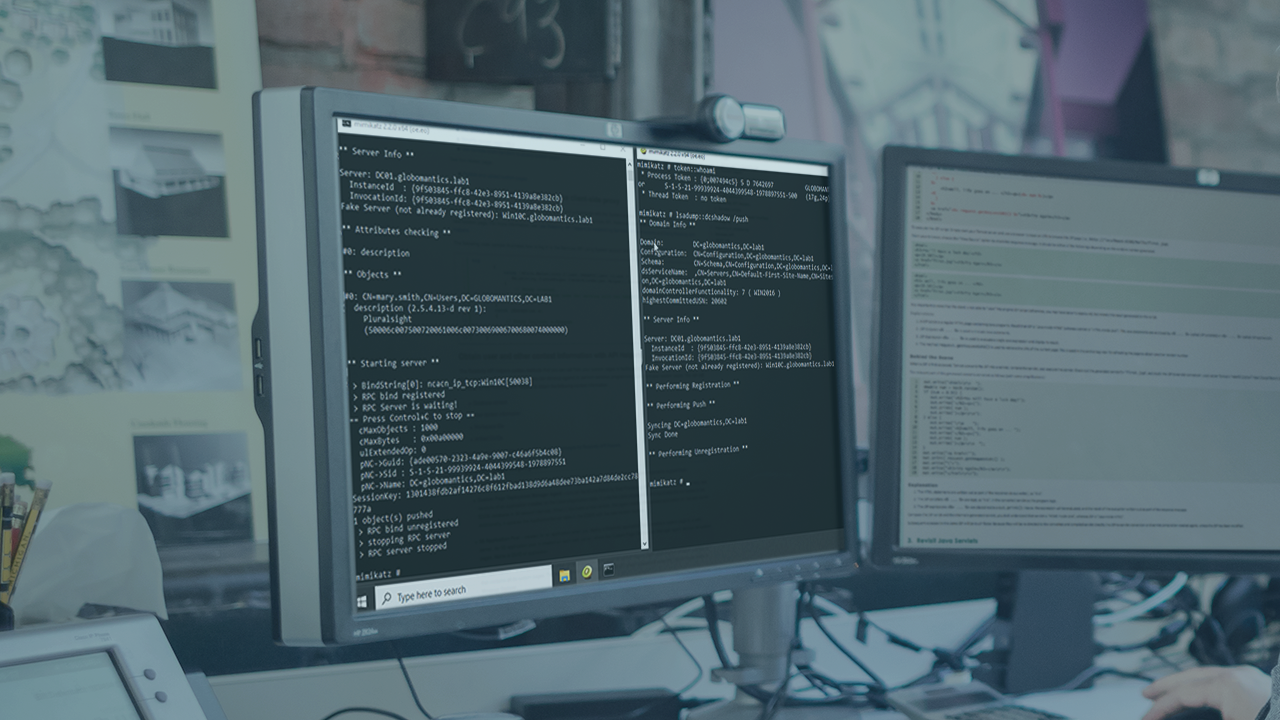
Lateral Movement with Mimikatz 2
Among other features, Mimikatz provides lateral movement capabilities such as pass the hash, user impersonation, and the creation of golden and silver tickets. Skill up your lateral movement techniques with Mimikatz.
- Course
Lateral Movement with Mimikatz 2
Among other features, Mimikatz provides lateral movement capabilities such as pass the hash, user impersonation, and the creation of golden and silver tickets. Skill up your lateral movement techniques with Mimikatz.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Would you like to move from system to system without clear text credentials? How about impersonating a domain controller to inject data of your choosing? In this course, Lateral Movement with Mimikatz 2, you will learn how to leverage the advanced lateral movement capabilities of the open-source Mimikatz project towards post-exploitation activities. First, you will see how to 'Pass the Hash' to authenticate without the need of a clear text password. Next, you will discover how Mimikatz is used to bypass the domain controllers with 'Pass the Ticket'. Finally, you will explore how to create golden and silver tickets to impersonate domain users and service accounts. When finished with this course, you will have the skills and knowledge of the open-source Mimikatz tool needed to emulate lateral movement techniques aligned with Mitre ATT&CK.

