- Course
Lateral Movement with PsExec
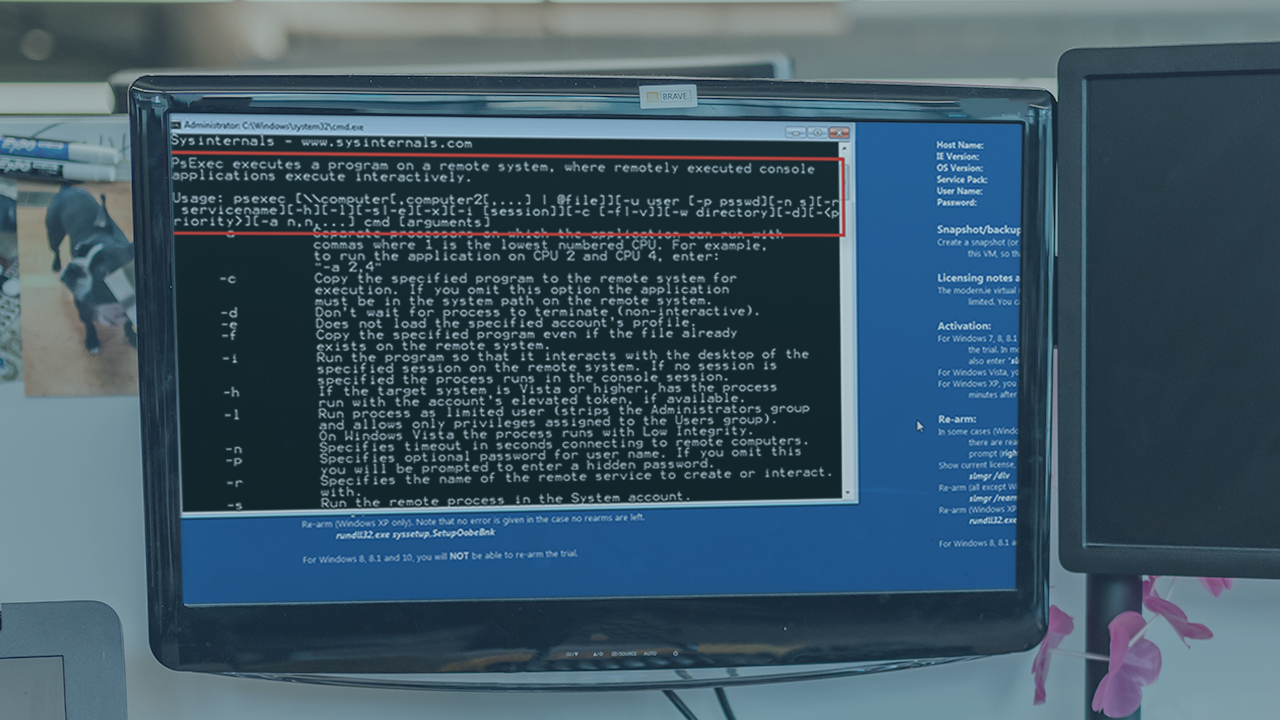
Learn to use PsExec to execute commands, programs, and laterally move to remote Windows hosts without installing additional software.
- Course
Lateral Movement with PsExec
Learn to use PsExec to execute commands, programs, and laterally move to remote Windows hosts without installing additional software.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Would you like to learn how to execute commands, programs, and open command prompts or PowerShell sessions on remote Windows hosts? In this course, Lateral Movement with PsExec, you will gain the ability to use PsExec to laterally move throughout a Windows domain from a host you already exploited. First, you will learn how to use PsExec to run commands on remote Windows hosts. Next, you will discover how to leverage PsExec to run programs remotely. Finally, you will explore how to laterally move throughout a Windows domain using PsExec. When you are finished with this course, you will have the skills and knowledge of PsExec needed to leverage it for lateral movement in a Windows domain.

