- Course
Malware Analysis: Identifying and Defeating Code Obfuscation
Malware authors routinely utilize obfuscation techniques to complicate the analysis of their code. This course will teach you techniques for identifying and defeating code obfuscation so that key characteristics and behaviors can be identified.
- Course
Malware Analysis: Identifying and Defeating Code Obfuscation
Malware authors routinely utilize obfuscation techniques to complicate the analysis of their code. This course will teach you techniques for identifying and defeating code obfuscation so that key characteristics and behaviors can be identified.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
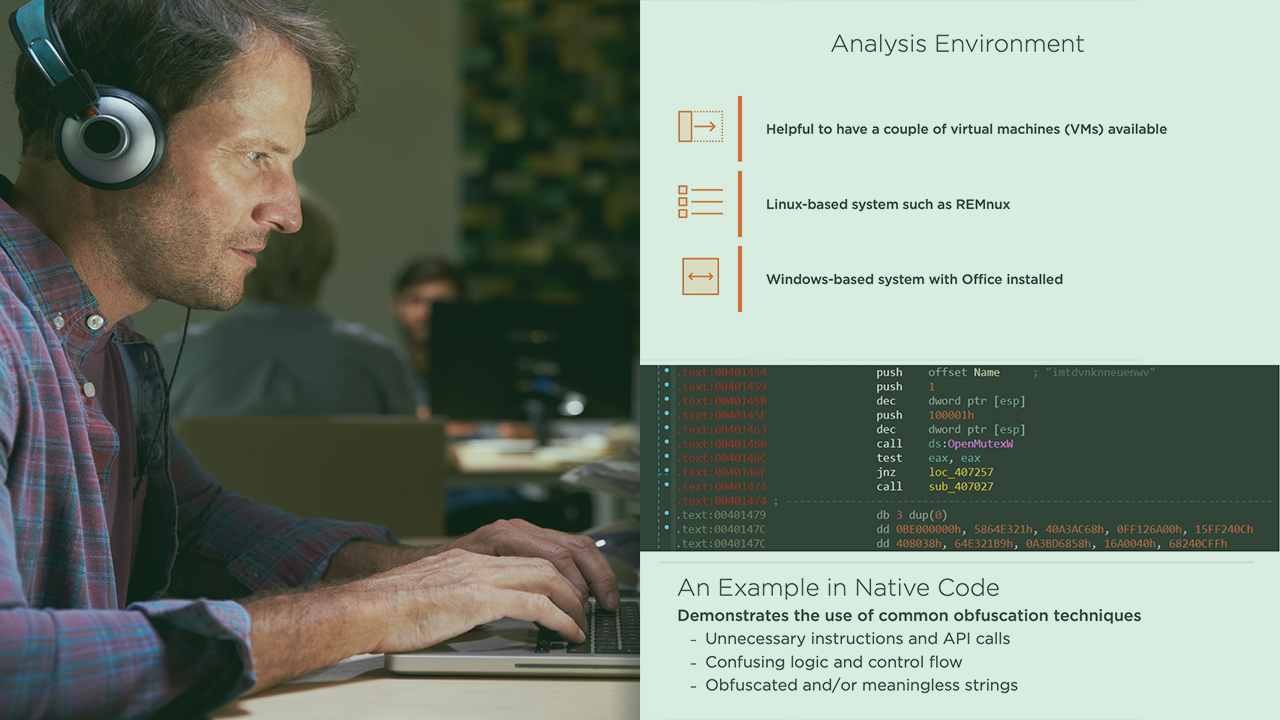
Malware authors will routinely utilize obfuscation techniques to complicate the analysis of their code. These techniques can prevent the discovery of important indicators of compromise and limit the ability to determine malware functionality. In this course, Malware Analysis: Identifying and Defeating Code Obfuscation, you will gain the skills necessary to not only identify prevalent obfuscation techniques, but also how to effectively defeat them. First, you will see how obfuscation will affect your analysis and effective strategies for defeating a variety of obfuscation methods. Next, you will explore how to identify and detect obfuscation techniques in interpreted code. This includes software routinely abused by malware authors such as Powershell and Visual Basic for Applications. You will next be able to expand your skills by learning about code obfuscation in native code. Finally, you will discover how malware authors use cryptography for obfuscation and ways to detect it. Each module of this course will include detailed demonstrations and hands-on labs that will allow you to analyze real-world malware. You will be going deep into malware obfuscation techniques with such tools as IDA Pro and WinDbg. By the end of this course, you will have the knowledge and skills to effectively tackle obfuscation!

