- Course
Metasploit Basics for Protecting SharePoint
Using Metasploit to Security Validate a SharePoint Environment.
- Course
Metasploit Basics for Protecting SharePoint
Using Metasploit to Security Validate a SharePoint Environment.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
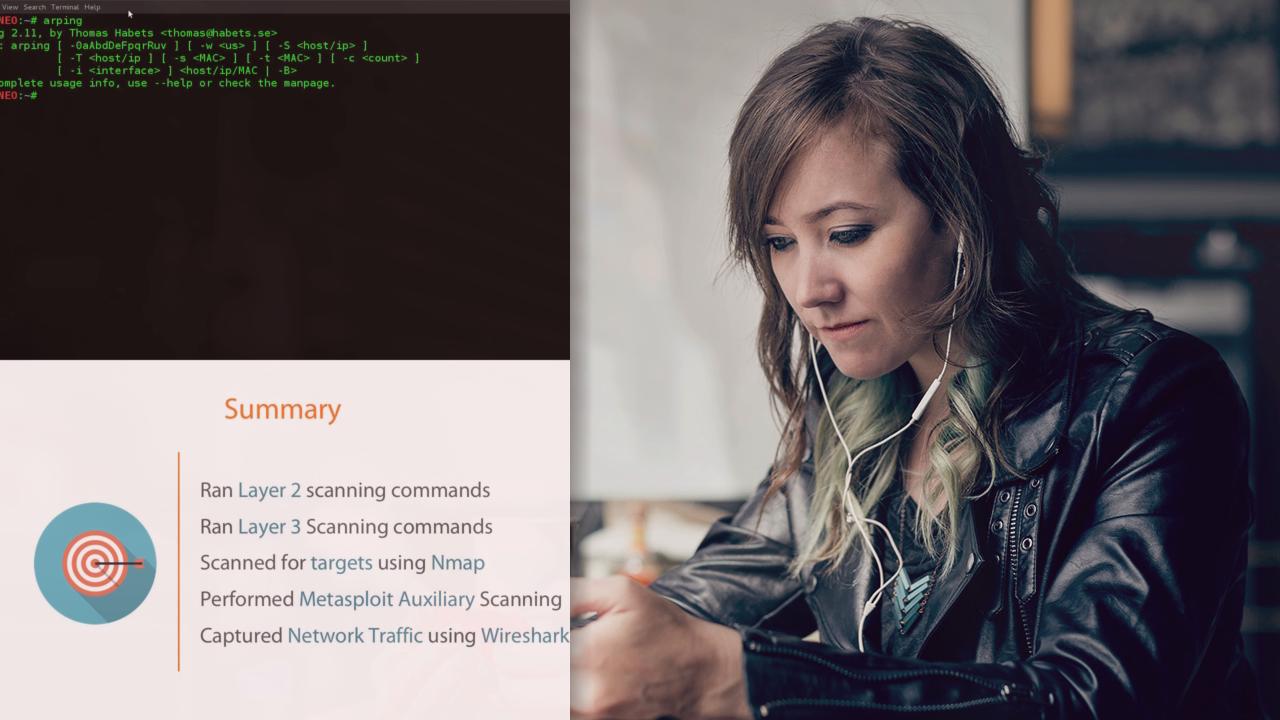
As an IT Administrator, your role is to ensure that the company SharePoint Environment is not only built correctly but also securely. SharePoint does not have a mechanism that notifies you how secure or insecure the system may be. Using Metasploit and some associated tools, you will be able to simulate attacks whether from inside or external to the network. This will allow you to know how secure your SharePoint Environment is, well until your users get access.

