- Course
Network Monitoring and Analysis
Pluralsight is not an official partner or accredited training center of EC-Council. This course covers network scanning and monitoring techniques to ensure optimal network performance and to identity network security breaches.
- Course
Network Monitoring and Analysis
Pluralsight is not an official partner or accredited training center of EC-Council. This course covers network scanning and monitoring techniques to ensure optimal network performance and to identity network security breaches.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
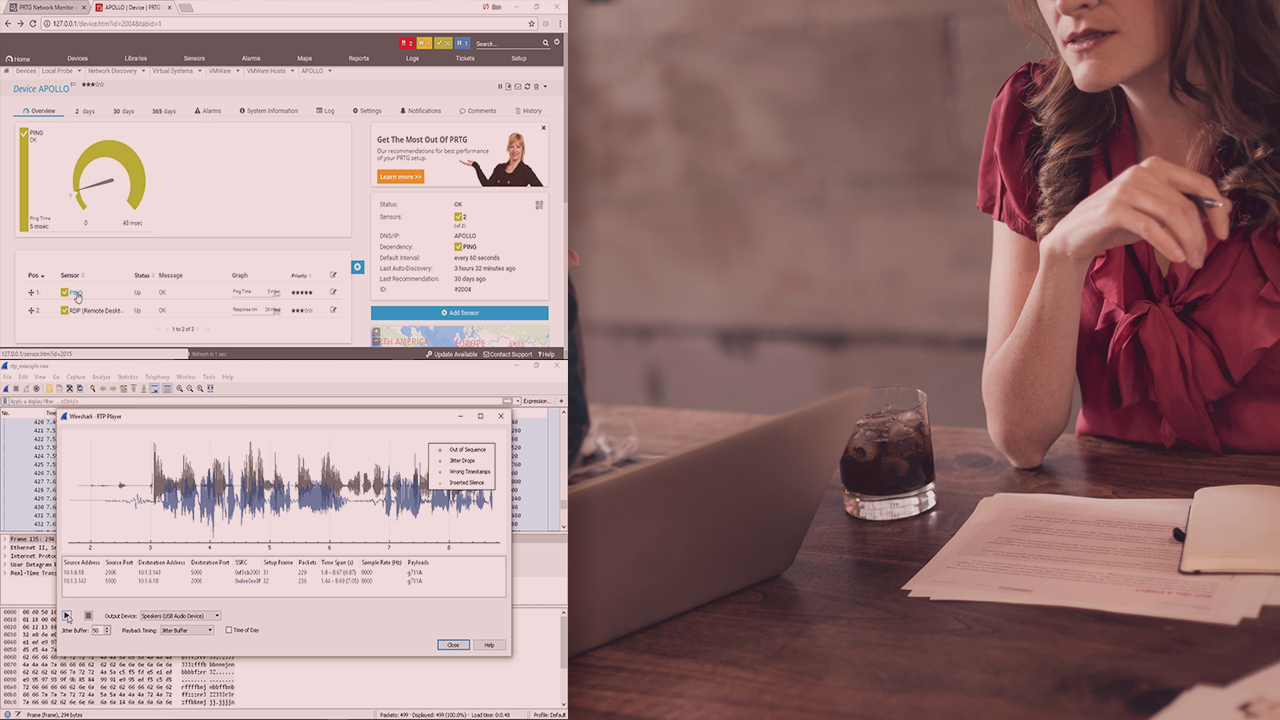
Pluralsight is not an official partner or accredited training center of EC-Council. Network scanning is performed by malicious users and IT security professionals. In this course, Network Monitoring and Analysis, you'll learn the fundamental knowledge of common network scans run by attackers so that you can detect this activity. First, you'll explore attack signatures, network monitoring techniques, and OS fingerprinting. Next, you'll learn about common TCP and UDP scan types and how ARP poisoning allows attackers to funnel traffic through their stations. Finally, you'll learn how to use the free, open source, Wireshark network analyzer to capture and analyze network traffic. When you're finished with this course, you will have the skills and knowledge of network monitoring needed to detect and protect against attackers.

