- Course
Securing Angular Apps with OpenID Connect and OAuth 2
OpenID Connect and OAuth 2 allow your apps to use modern security protocols and to participate in a Single Sign-on (SSO) experience across multiple apps. This course will show you how to authenticate users and authorize access in your Angular apps.
- Course
Securing Angular Apps with OpenID Connect and OAuth 2
OpenID Connect and OAuth 2 allow your apps to use modern security protocols and to participate in a Single Sign-on (SSO) experience across multiple apps. This course will show you how to authenticate users and authorize access in your Angular apps.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
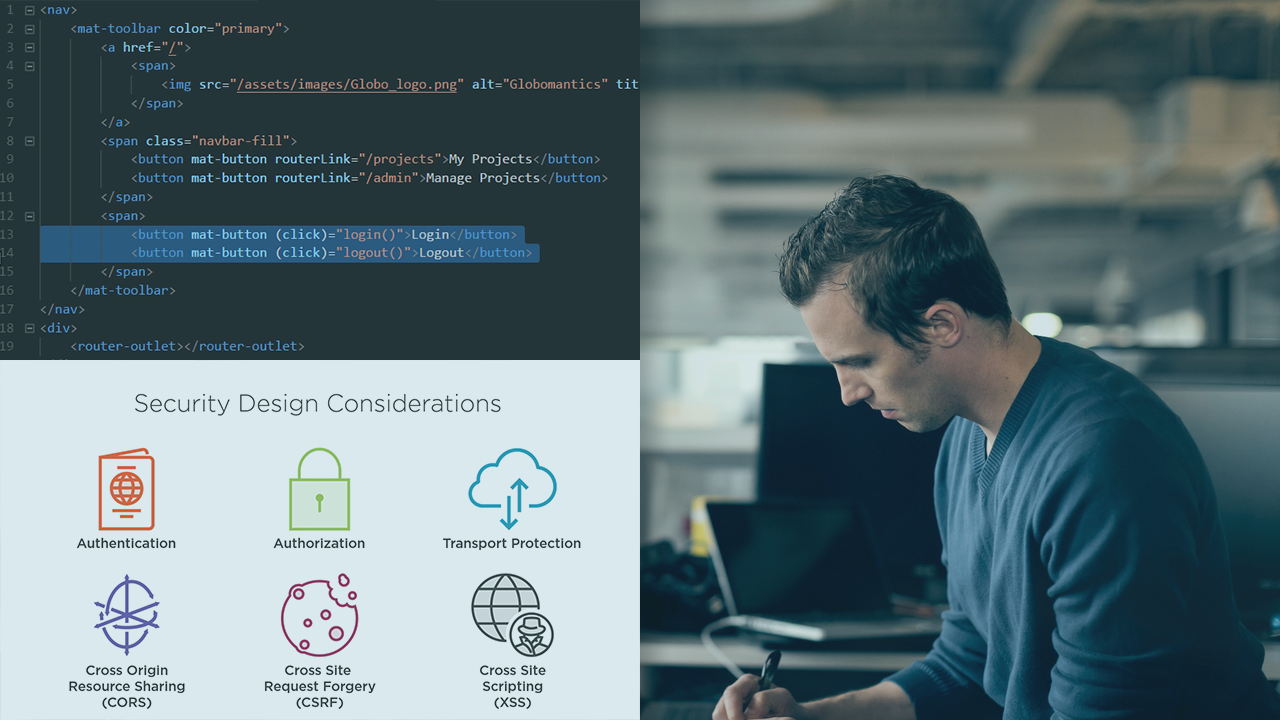
Securing your Angular apps with modern, interoperable security protocols helps you ensure your apps are secure, and that they can participate in a Single Sign-on (SSO) experience across multiple apps that use the same identity provider. In this course, Securing Angular Apps with OpenID and OAuth 2, you will learn how to apply the OpenID Connect and OAuth 2 protocols to authenticate users and authorize their access to functionality and data in your apps. First, you will explore the security fundamentals and concepts you need to be aware of for Angular apps. Next, you will discover how to connect to your OpenID Connect identity provider for authentication. Lastly, you will successfully use and manage your OAuth 2 access tokens for authorization. When you are finished with this course, you will have a solid foundation for building your Angular apps with robust security and done in a way that lets you integrate with any OpenID Connect and OAuth 2 identity provider.
Securing Angular Apps with OpenID Connect and OAuth 2
-
Introduction | 4m 6s
-
Security Design Considerations | 6m 20s
-
Client vs. Server Security | 1m 42s
-
Angular App Security Architecture | 1m 53s
-
Authentication and Authorization | 3m 32s
-
Terminology | 3m 15s
-
OpenID Connect and OAuth 2 Protocols | 2m 12s
-
Identity Provider Options | 5m 12s
-
Client Library Options | 2m 5s
-
A Tour through the Demo Application | 3m 44s

