- Course
What's New in the OWASP Top 10 for 2013
The OWASP Top 10 Web Application Security Risks is the first stop for web developers who are serious about securing their online creations. This course outlines what has changed in web security since the previous 2010 edition, and where developers should now focus their security efforts.
- Course
What's New in the OWASP Top 10 for 2013
The OWASP Top 10 Web Application Security Risks is the first stop for web developers who are serious about securing their online creations. This course outlines what has changed in web security since the previous 2010 edition, and where developers should now focus their security efforts.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
The Top 10 Web application security risks produced by OWASP is an evolving resource that helps organizations focus on the most prominent risks in web security today. Every few years we see a revision; the types of attacks we’re witnessing change, the defenses change, and the risk and associated priority changes. OWASP adapts to this changing environment and recently made available the 2013 edition of the Top 10. This course is designed to help those who already have an awareness of the Top 10 understand what’s new in the latest edition and how the landscape has changed in three short years. It also introduces the concept of "Risk Assessments" and provides further resources to help go beyond just the Top 10 risks.
What's New in the OWASP Top 10 for 2013
-
It's All About Risks | 1m 45s
-
Where Does the Data on Risks Come From? | 1m 32s
-
What Are Application Security Risks? | 3m 29s
-
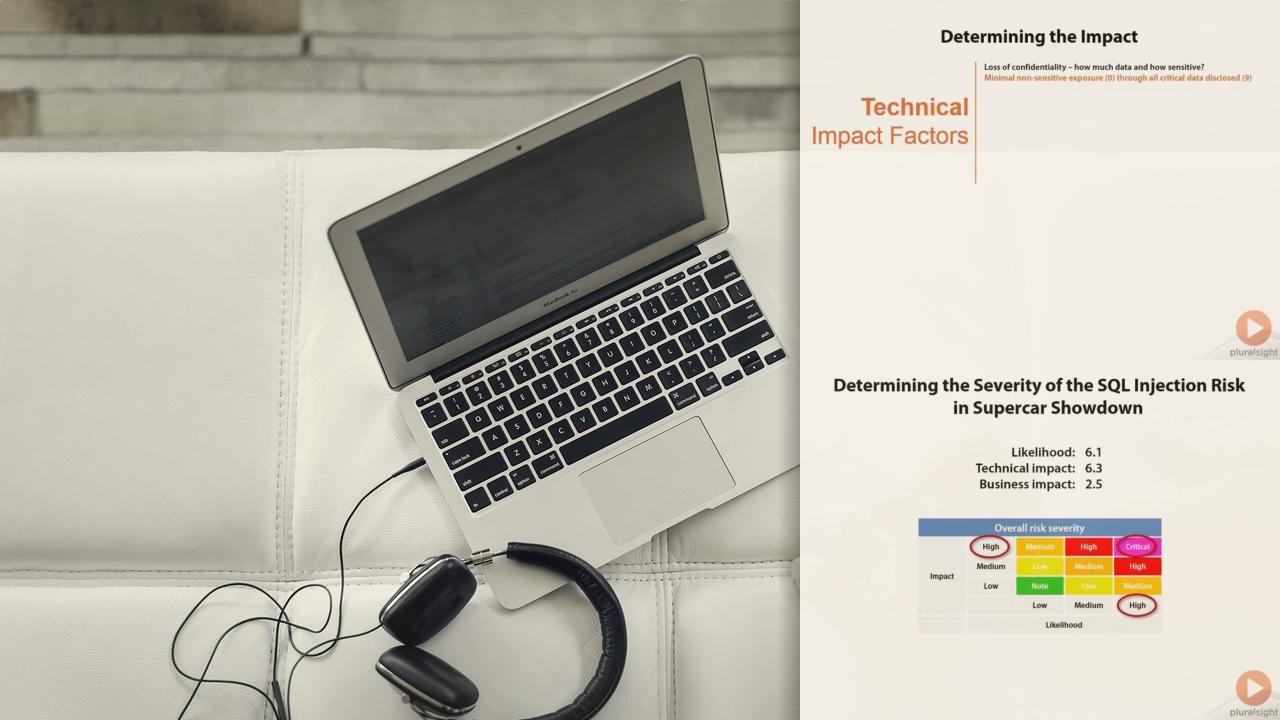
The OWASP Risk Rating Methodology | 3m 36s
-
Understanding Likelihood | 4m 14s
-
Assessing Likelihood | 4m 54s
-
Understanding Impact | 3m 37s
-
Assessing Impact | 3m 5s
-
Calculating the Overall Risk | 2m 4s
-
Applying the Methodology to the XSS Risk | 4m 32s
-
Summary | 2m 48s

