- Course
PCI DSS: Restricting Access to Cardholder Data
Requirements 7, 8 & 9 of PCI DSS version 3.2.1 are to Implement Strong Access Control Measures for logical and physical cardholder data. You'll understand what each requirement asks for and discover practical guidance from experienced PCI assessors.
- Course
PCI DSS: Restricting Access to Cardholder Data
Requirements 7, 8 & 9 of PCI DSS version 3.2.1 are to Implement Strong Access Control Measures for logical and physical cardholder data. You'll understand what each requirement asks for and discover practical guidance from experienced PCI assessors.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
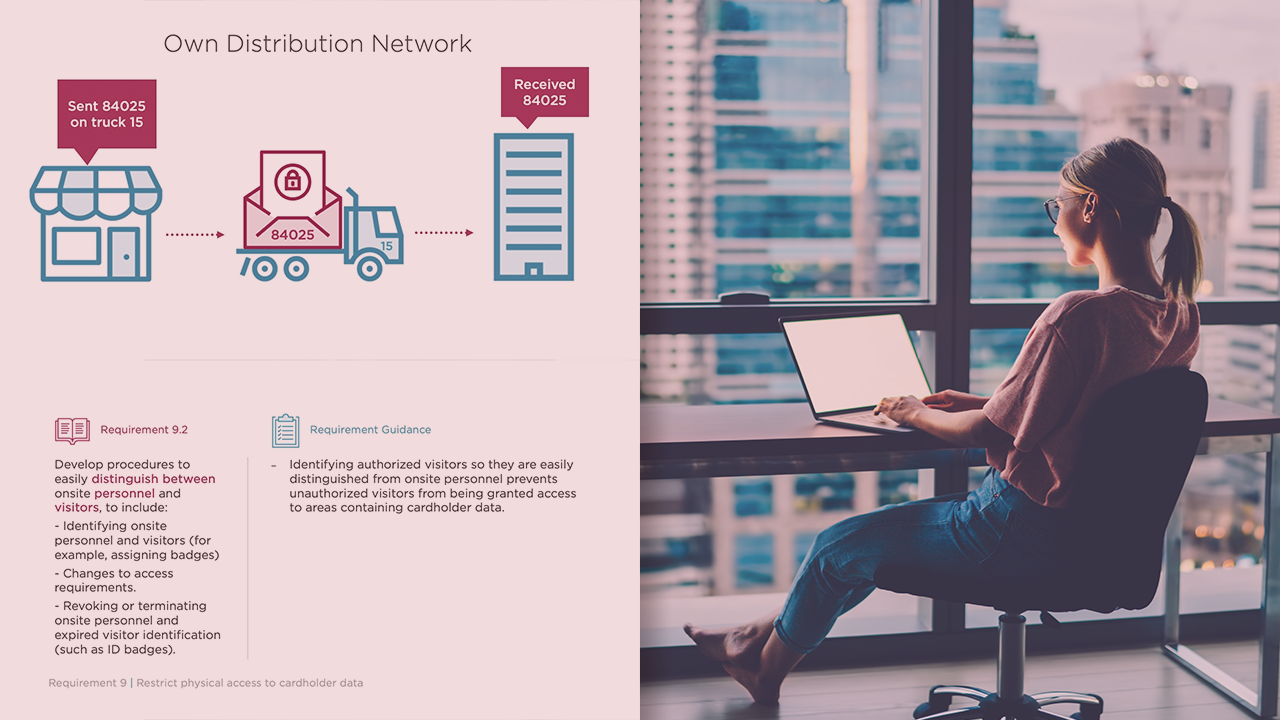
The key to achieving PCI DSS compliance is a thorough knowledge of each of the sub-requirements and how they will be assessed. In this course, PCI DSS: Restricting Access to Cardholder Data, you’ll learn how to interpret PCI DSS requirements 7, 8 & 9, and apply them to your organization. First, you’ll learn how PCI DSS wants role-based access and based on least privilege and need to know. Next, you’ll explore the long and prescriptive requirements about username, passwords and multi-factor authentication. Then you’ll take a look at the requirements related to the protection of cardholder data in physical format – written in paper and saved to electronic media. Finally, you’ll discover practical insights about both requirements from experienced PCI assessors. When you’ve finished with this course you will have the skills and knowledge to apply PCI DSS requirements 7, 8 and 9 to any organization’s environment and to determine whether it is compliant with the demands of the standard.
PCI DSS: Restricting Access to Cardholder Data
-
Navigating the PCI DSS Standards | 5m 44s
-
Requirement 7.1 | 4m 10s
-
Requirement 7.2 | 1m 26s
-
Requirement 7.3 | 42s
-
Strategies for Success with Requirement 7 | 4m 46s
-
Where Requirement 7 Goes Wrong | 46s
-
What Is an Access Control System? | 1m 54s
-
The Second QSA Assessment, Compromises, and Compensating Controls | 2m 28s

