- Course
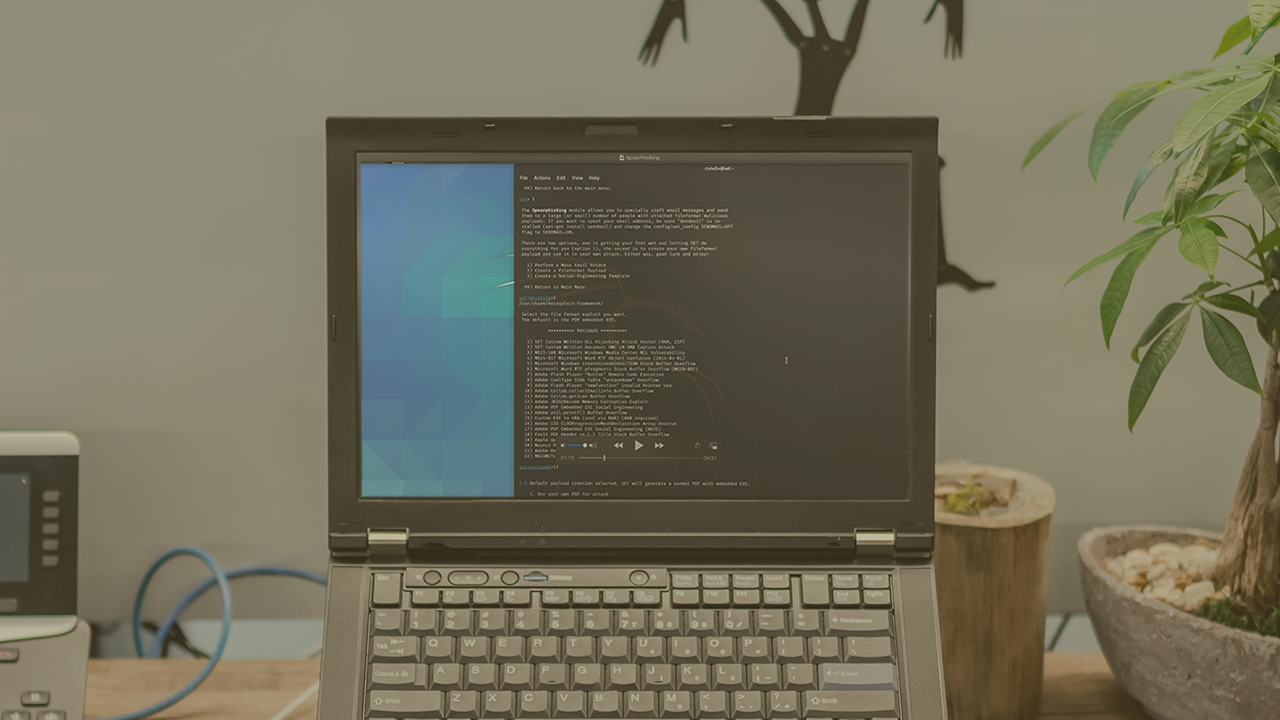
People Information Gathering with the Social Engineering Toolkit (SET)
Social Engineering is one of the most common attack vectors. Unfortunately, in this digital age, many people still fall victim to these attacks. In this course, you will learn Initial Access using the Social Engineering Toolkit.
- Course
People Information Gathering with the Social Engineering Toolkit (SET)
Social Engineering is one of the most common attack vectors. Unfortunately, in this digital age, many people still fall victim to these attacks. In this course, you will learn Initial Access using the Social Engineering Toolkit.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Social engineering assesses people, processes, and procedures by using attack vectors such as email, malicious wireless networks and more in the attempt to breach organizational safeguards. In this course, People Information Gathering with the Social Engineering Toolkit (SET), you will cover how to utilize the Social Engineer Toolkit for Initial Access in a red team environment. First, you will demonstrate the ability to craft social engineering attacks such as spear phishing using various payloads. Next, you will work with other attack vectors within the Social Engineer Toolkit which relates to malicious payloads and integration into Metasploit. Finally, you will be able to simulate a social engineering attack. When you are finished with this course, you will have the skills and knowledge to execute these techniques these techniques: Conduct Social Engineering (T1268) and Spearphishing for information (T1397) using the Social Engineer Toolkit.

