- Course
Planning, Deploying, and Configuring Splunk Enterprise Security
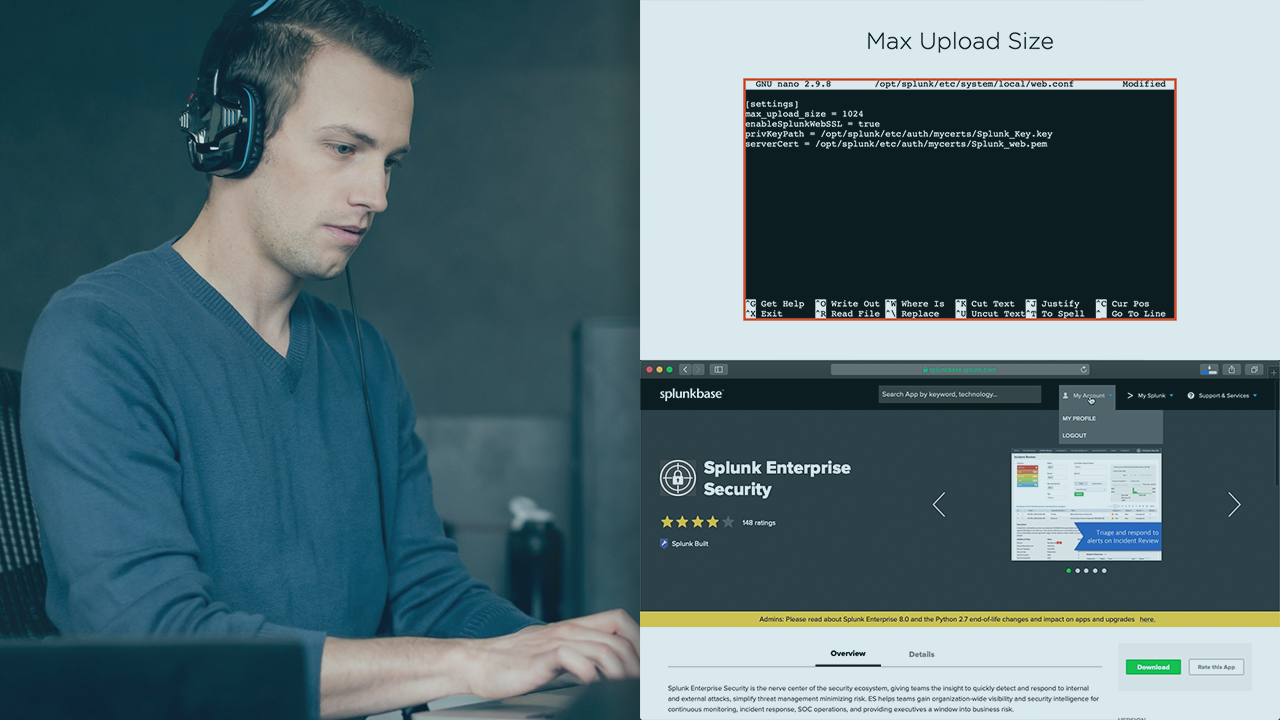
Splunk Enterprise Security is a premium application used within the Splunk deployment to help with SOC operations. This course will teach you how to plan for, design, and deploy the application to use in your environment.
- Course
Planning, Deploying, and Configuring Splunk Enterprise Security
Splunk Enterprise Security is a premium application used within the Splunk deployment to help with SOC operations. This course will teach you how to plan for, design, and deploy the application to use in your environment.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Splunk Enterprise Security (ES) solves many problems within our SOCs including efficient operations. In this course, Planning, Deploying, and Configuring Splunk Enterprise Security, you’ll learn how to get this application installed and configured quickly. First, you’ll explore the design process and learn how all of the design considerations in a Splunk ES deployment. Next, you’ll discover how to prepare your environment for a Splunk Enterprise Security deployment. Finally, you’ll learn how to configure the tool and all of the applicable data modifications you’ll need to make. When you’re finished with this course, you’ll have the skills and knowledge of Splunk Enterprise Security needed to get it up and running.
Planning, Deploying, and Configuring Splunk Enterprise Security
-
Introduction | 2m 26s
-
Course Overview | 2m 22s
-
Indexer Functionality and Design | 2m 35s
-
Designing a Splunk Enterprise Security Deployment | 3m 31s
-
Ingesting Data into Splunk Enterprise Security | 5m 13s
-
Data Models and Acceleration Overview | 6m 25s
-
Splunk Enterprise Security Requirements | 2m 27s
-
Other Design Considerations | 4m 6s

