- Course
Post Exploitation: Pillaging and Data Exfiltration
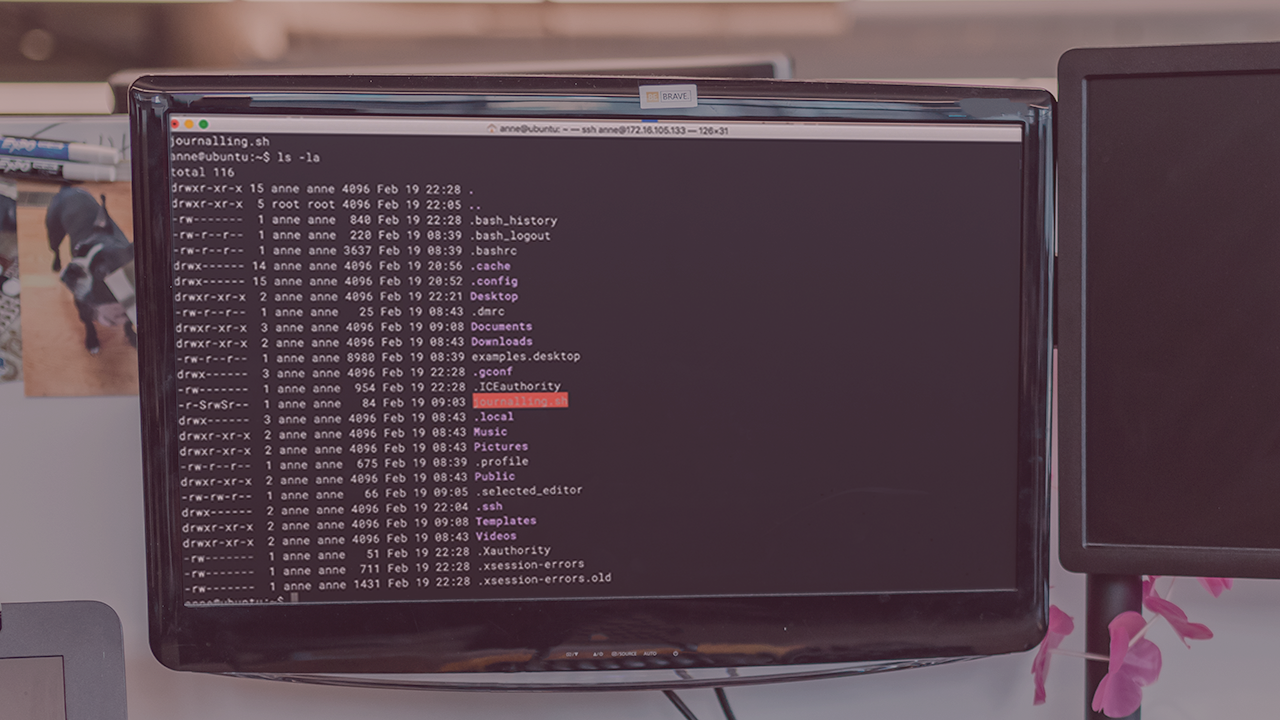
The simplest stage in a penetration test is data exfiltration, or is it? With the advent of new types of attackers, testing this is more critical than ever before. In this course, you'll explore some of the processes involved in this stage.
- Course
Post Exploitation: Pillaging and Data Exfiltration
The simplest stage in a penetration test is data exfiltration, or is it? With the advent of new types of attackers, testing this is more critical than ever before. In this course, you'll explore some of the processes involved in this stage.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Safeguarding a network today requires a multiple stage approach, not only is it important to keep attackers out, but it is also important to keep data from leaving the network. This means that we need to begin looking at data exfiltration not just as a stage in the penetration test, but as a more comprehensive solution that requires more robust checks from the client to lock down. In this course, Post Exploitation: Pillaging and Data Exfiltration, you’ll gain the ability to evaluate the systems not just for the data that they may possess through pillaging, but also begin to look at each system as another step in a long chain that can be leveraged to exfiltration. First, you’ll explore pillaging, critically evaluating the value of the system with pre-determined parameters. Next, you’ll discover how to chain multiple attacks together to create the final path for data exfiltration, touching upon bypassing some modern protection mechanisms. Finally, you’ll learn how to ask yourself the questions that will enable you to create your own processes. When you’re finished with this course, you’ll have the skills and knowledge of pillaging and data exfiltration needed to create, build, and execute attacks upon networks in a manner that will enable you to create a report that has value to your clients.

