- Course
Practical Encryption and Cryptography Using Python
Security is vastly important in today's world. This course teaches you how to use cryptography in practice and how to apply it in Pythonrse.
- Course
Practical Encryption and Cryptography Using Python
Security is vastly important in today's world. This course teaches you how to use cryptography in practice and how to apply it in Pythonrse.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
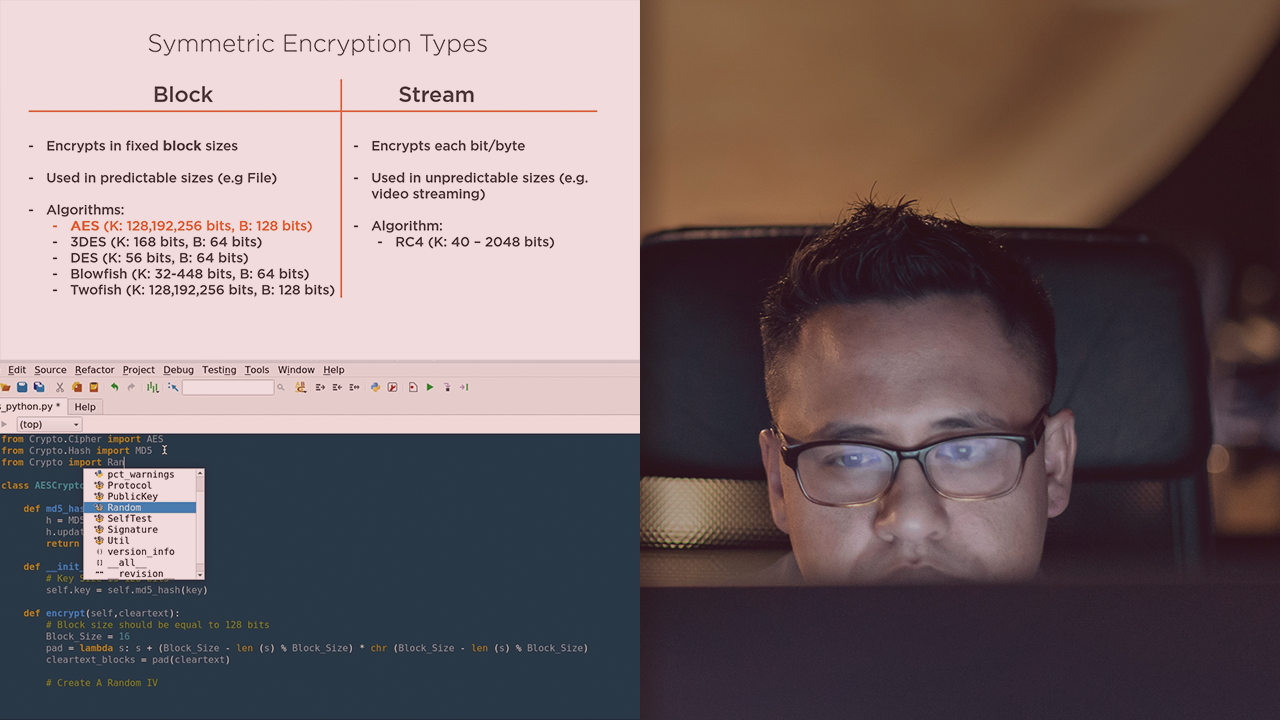
Security is vastly important in today's world. In this course, Practical Encryption and Cryptography Using Python, you will learn the practical aspect of cryptography using the amazing programming language Python, and you will gain the confidence to master the skill of crypto by using real-life examples. First, you will learn about hashing algorithms. Next, you will discover Symmetric Encryption using Python. Finally, you will explore the multiple angles of Asymmetric Encryption using public and private keys. When you're finished with this course, you will have the necessary skills and knowledge about cryptography to use in your career.

