- Course
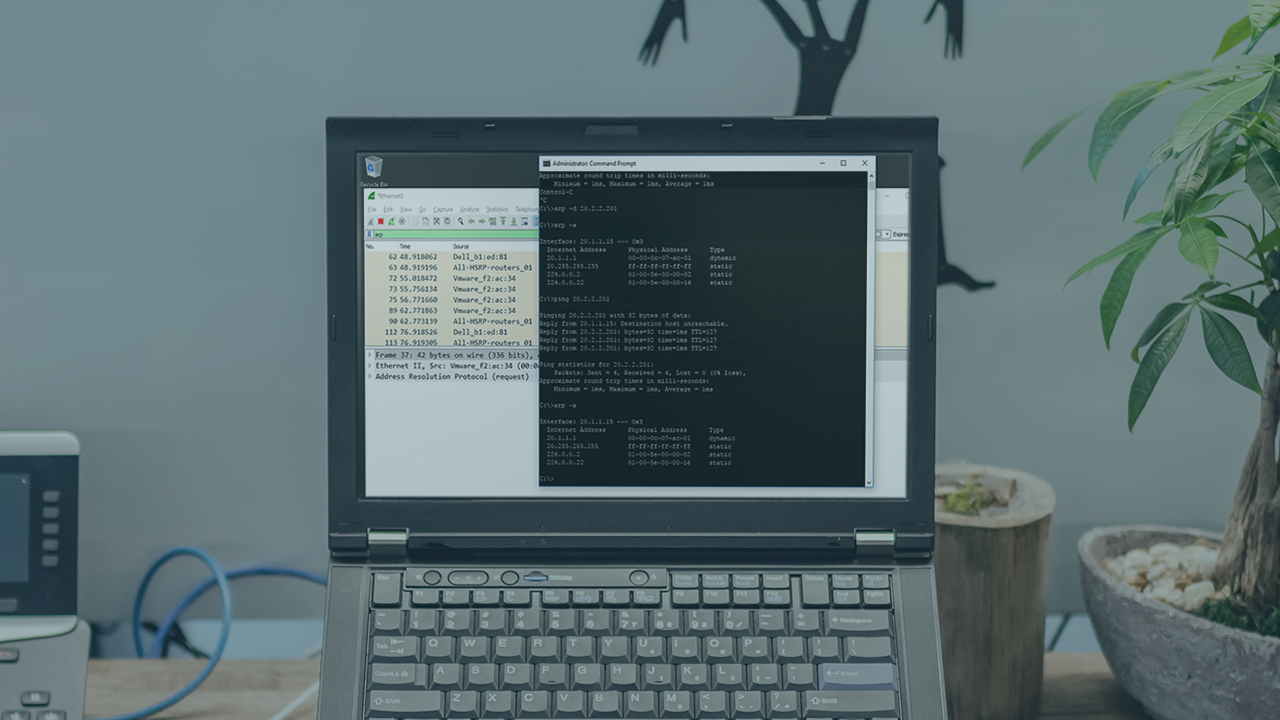
Protocol Deep Dive: Address Resolution Protocol (ARP)
Address Resolution Protocol (ARP) is essential for computer communication across the network. This course provides the in-depth knowledge needed to understand, improve, troubleshoot, and secure ARP-related communications in your network.
- Course
Protocol Deep Dive: Address Resolution Protocol (ARP)
Address Resolution Protocol (ARP) is essential for computer communication across the network. This course provides the in-depth knowledge needed to understand, improve, troubleshoot, and secure ARP-related communications in your network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Address Resolution Protocol (ARP) is foundational for nearly all LAN communication. Because ARP and its variations are so widely relied upon, a deep understanding of ARP is necessary to support network communications, troubleshoot interoperability issues, and improve the efficiency of networks. Furthermore, it is critically important that you understand its nature so you can reduce and prevent related cyber threats. In this course, Protocol Deep Dive: Address Resolution Protocol (ARP), you will learn ARP from the ground up, including every part of Address Resolution Protocol messages, their functions and variations, and their security risks. First, you will learn how to capture ARP and use those captures to identify ARP messaging and troubleshoot ARP-related problems. Next, you will explore the details of every major ARP variation, learning how they apply to network communications. Finally, you will examine best practices and procedures you can apply to common LAN ARP-based attacks. By the end of this course, you will be able to clearly identify how ARP communications are used, when and how they might cause problems or security risks, and which solutions are appropriate in any given scenario.

