- Course
Reconnaissance with Shodan
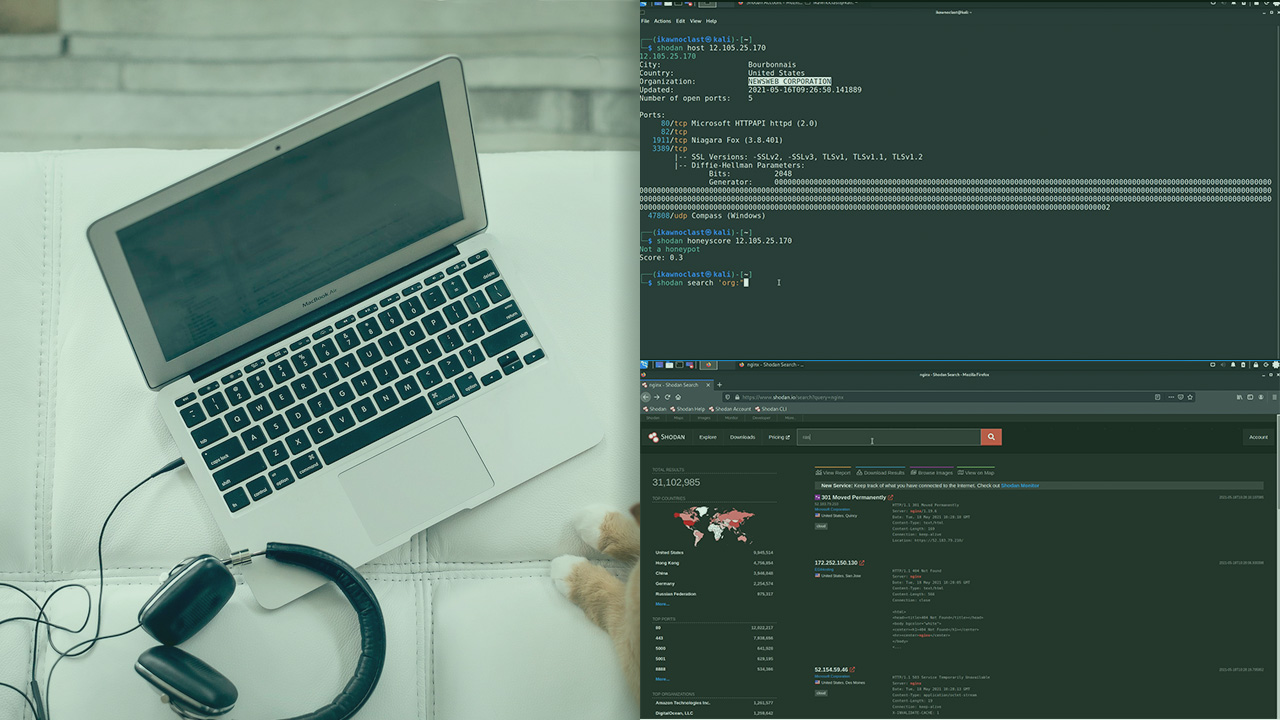
Shodan is a search engine that continuously scans the internet identifying internet-connected devices and can be used to plan future red team operations. In this course, you will learn Reconnaissance using Shodan.
- Course
Reconnaissance with Shodan
Shodan is a search engine that continuously scans the internet identifying internet-connected devices and can be used to plan future red team operations. In this course, you will learn Reconnaissance using Shodan.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
When planning future operations, a red team needs information about the target organization. Specifically, details about the organization’s internet-connected devices, their software, services, IP addresses, and locations can be leveraged to plan and execute other phases of the adversary life cycle. In this course, Reconnaissance with Shodan, I’ll cover how to utilize Shodan to execute reconnaissance in a red team environment. First, I’ll demonstrate how to identify devices associated with a specific organization. Next, I’ll apply search filters for refine the information to specific software and versions. Finally, I’ll simulate reviewing specific device information as a potential attack target. When you’re finished with this course, you’ll have the skills and knowledge to execute MITRE ATT&CK techniques, such as T1592 Gather Victim Host Information, T15960 Gather Victim Network Information, and T1596 Search Open Technical Databases, using Shodan. More importantly, knowing how these techniques can be used against you, will ultimately lend to your ability as an organization, or an individual, to detect and defend against specific attack vectors.

