- Course
Getting Started with Reverse Engineering
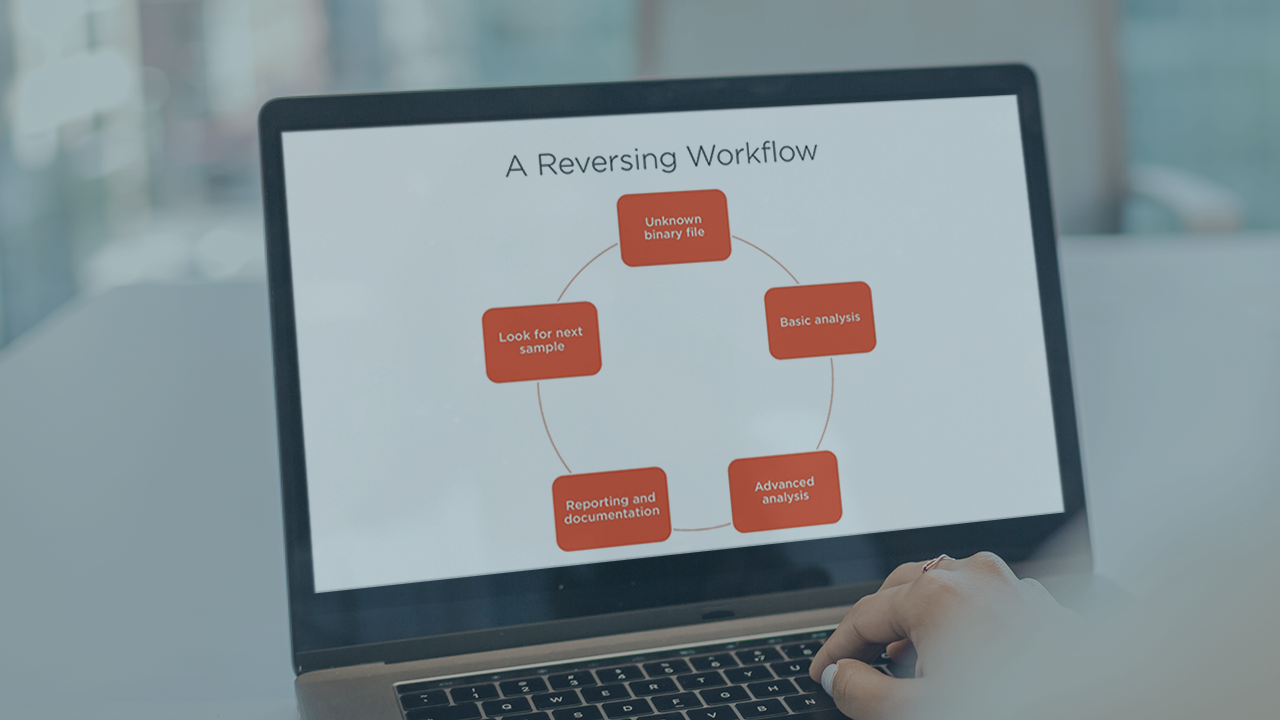
Reverse engineering binary code is a core skill for software security engineers, malware analysts and penetration testers. This course will teach you techniques for reversing binary code to identify program characteristics and behavior.
- Course
Getting Started with Reverse Engineering
Reverse engineering binary code is a core skill for software security engineers, malware analysts and penetration testers. This course will teach you techniques for reversing binary code to identify program characteristics and behavior.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
The ability to reverse engineer binary code is an essential skill for anyone responsible for software security or performing malware analysis, and it even plays a significant role in performing penetration tests and incident response. In this course, Getting Started with Reverse Engineering, you will gain the skills necessary to reverse engineer native code and determine program behavior. First, you will discover the basic elements of modern CPU architecture and the essentials of assembly language. Next, you will learn about native code, the portable executable file format and techniques to enrich your reverse engineering efforts. Finally, you will explore proficiency in the tools and techniques associated with performing static and dynamic reverse engineering to include IDA Pro and WinDbg. Throughout this course you will be able to follow along through comprehensive demonstrations and apply yourself through hands-on labs. By the end of this course, you will have the knowledge and skills necessary to reverse engineer native code binaries.

