- Course
Running the Business of Information Security
Security is not only about protecting assets, managing risk, and ensuring compliance. It’s also a business process. This course will give you the advanced knowledge you need to effectively manage the business of security.
- Course
Running the Business of Information Security
Security is not only about protecting assets, managing risk, and ensuring compliance. It’s also a business process. This course will give you the advanced knowledge you need to effectively manage the business of security.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
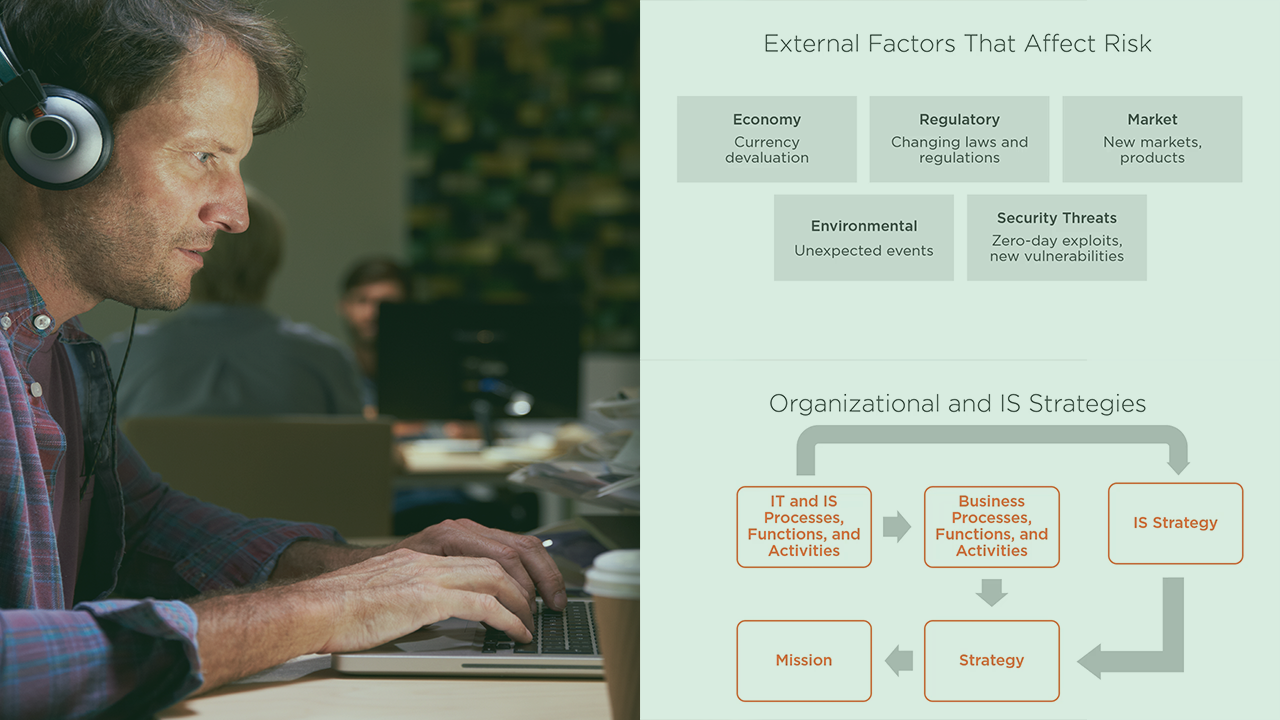
Most people know that information security is about protecting information systems and data, managing cyber risk, and ensuring compliance with governance. However, the security function of a business is also a business function unto itself. It is managed like any other business function, whether it involves staffing with qualified personnel, tracking projects, or managing the security budget. In this course, Running the Business of Information Security, you will learn your key to getting the focused knowledge you need to have, both for the real world and advanced certification exams. First, you’ll explore preparing budget requests based upon programmed organizational security needs. You’ll also learn how to manage the security budget and other resources to their maximum effectiveness. Next, this course will show you how to create business cases to justify security investments and expenditures to support the business mission and goals. You’ll also learn how to manage a dynamic budget based upon changing cybersecurity and business risk. Finally, you’ll discover how to prepare, present, and report security budget status to include expenditures, investments, and other critical budget information. By the end of this course, you’ll have the advanced knowledge you need to help you manage the cybersecurity program’s budget in your organization, as well as to help pass advanced cybersecurity management certification exams.
Running the Business of Information Security
-
Organizational Strategy and Information Securty | 4m 36s
-
Business Processes and Functions | 1m 59s
-
Information Security Functions and Processes | 1m 38s
-
Relationships between Information Security and Business Functions | 3m
-
Integrating Information Security into Organizational Processes | 3m 58s
-
Scenario: Organizational Characteristics of Globomantics | 2m 44s
-
Summary | 58s


